During the Summer of 2024, I had a talk at Troopers called “A Decade of Active Directory Attacks:What We’ve Learned & What’s Next” (Slides & Video) where I focused on the key milestones of Active Directory security (history). This article covers my “decade of Active Directory attacks” in some detail which was correlated with public …
Tag: PowerView
Aug 15 2016
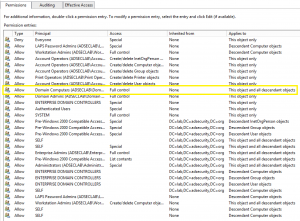
Microsoft LAPS Security & Active Directory LAPS Configuration Recon
Over the years, there have been several methods attempted for managing local Administrator accounts: Scripted password change – Don’t do this. The password is exposed in SYSVOL. Group Policy Preferences. The credentials are exposed in SYSVOL. Password vault/safe product (Thycotic, CyberArk, Lieberman, Quest, Exceedium, etc). Microsoft Local Administrator Password Solution (LAPS). LAPS Overview Microsoft’s …
Aug 13 2016
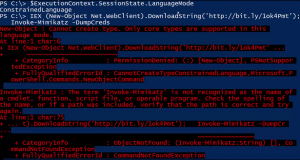
PowerShell Security: PowerShell Attack Tools, Mitigation, & Detection
This post is a follow-up of sorts from my earlier posts on PowerShell, my PowerShell presentation at BSides Baltimore, and my presentation at DEF CON 24. Hopefully this post provides current information on PowerShell usage for both Blue and Red teams. Related posts: BSides Charm Presentation Posted: PowerShell Security: Defending the Enterprise from the Latest …
Apr 24 2016
BSides Charm Presentation Posted: PowerShell Security: Defending the Enterprise from the Latest Attack Platform
This was my second year speaking at BSides Charm in Baltimore. Last year I spoke about Active Directory attack & defense and it was my first time speaking at a conference. 🙂 The presentation slides for my talk “PowerShell Security: Defending the Enterprise from the Latest Attack Platform” are now on the Presentations tab here …
Nov 22 2015
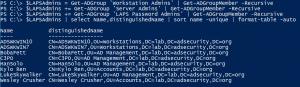
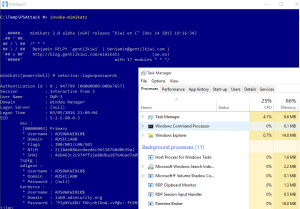
Dump Clear-Text Passwords for All Admins in the Domain Using Mimikatz DCSync
The two key goals of any attack is access and persistence. This post covers elements of each. In a post-exploitation scenario where the attacker has compromised the domain or an account with delegated rights, it’s possible to dump the clear-text passwords of admins without being a Domain Admin*. This method requires the Active Directory Domain …


Recent Comments