In late 2014, I discovered that the domain field in many events in the Windows security event log are not properly populated when forged Kerberos tickets are used. The key indicator is that the domain field is blank or contains the FQDN instead of the short (netbios) name and depending on the tool used to …
Tag: GoldenTicket
Dec 31 2015
Cracking Kerberos TGS Tickets Using Kerberoast – Exploiting Kerberos to Compromise the Active Directory Domain
Microsoft’s Kerberos implementation in Active Directory has been targeted over the past couple of years by security researchers and attackers alike. The issues are primarily related to the legacy support in Kerberos when Active Directory was released in the year 2000 with Windows Server 2000. This legacy support is enabled when using Kerberos RC4 encryption …
Nov 17 2015
How Attackers Use Kerberos Silver Tickets to Exploit Systems
Usually Golden Tickets (forged Kerberos TGTs) get all the press, but this post is about Silver Tickets and how attackers use them to exploit systems. I have talked about how Silver Tickets can be used to persist and even re-exploit an Active Directory enterprise in presentations at security conferences this year. This post continues this …
Aug 07 2015
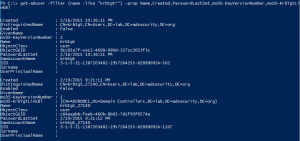
Kerberos Golden Tickets are Now More Golden
At my talk at Black Hat USA 2015, I highlighted new Golden Ticket capability in Mimikatz (“Enhanced Golden Tickets”). This post provides additional detailed on “enhanced” Golden Tickets. Over the past few months, I researched how SID History can be abused in modern enterprises. As part of this research, I reached out to Benjamin Delpy, …
Aug 02 2015
DEF CON 23 (2015) Red vs Blue: Modern Active Directory Attacks & Defense Talk Detail
This week at DEF CON 23, I will be speaking about Active Directory attack & defense in my talk “Red vs Blue: Modern Active Directory Attacks & Defense”. This is the 4th iteration of this talk and includes the latest updates to attack methods and defensive strategies.This DEF CON version has a new segment I …
Jul 26 2015
Black Hat USA 2015 Red vs Blue Active Directory Attack & Defense Talk Detail
Next week at Black Hat USA 2015, I will be speaking about Active Directory attack & defense in my talk “Red vs Blue: Modern Active Directory Attacks Detection and Protection”. This is the 3rd iteration of this talk and includes the latest updates to attack methods and defensive strategies. I’m including lots of updates and …
May 03 2015
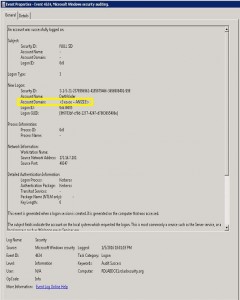
Detecting Forged Kerberos Ticket (Golden Ticket & Silver Ticket) Use in Active Directory
Over the last 6 months, I have been researching forged Kerberos tickets, specifically Golden Tickets, Silver Tickets, and TGTs generated by MS14-068 exploit code (a type of Golden Ticket). I generated forged Kerberos tickets using Mimikatz (Mimikatz Command Reference) and MS14-068 exploits and logged the results. Over the course of several weeks, I identified anomalies …
Nov 22 2014
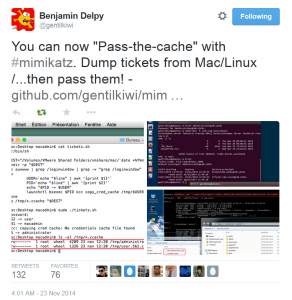
Mimikatz and Active Directory Kerberos Attacks
NOTE: While this page will remain, the majority of the Mimikatz information in this page is now in the “Unofficial Mimikatz Guide & Command Reference” which will be updated on a regular basis. Mimikatz is the latest, and one of the best, tool to gather credential data from Windows systems. In fact I consider Mimikatz …
Nov 10 2014
Kerberos & KRBTGT: Active Directory’s Domain Kerberos Service Account
Every Domain Controller in an Active Directory domain runs a KDC (Kerberos Distribution Center) service which handles all Kerberos ticket requests. AD uses the KRBTGT account in the AD domain for Kerberos tickets. The KRBTGT account is one that has been lurking in your Active Directory environment since it was first stood up. Each Active …



Recent Comments