Microsoft’s Kerberos implementation in Active Directory has been targeted over the past couple of years by security researchers and attackers alike. The issues are primarily related to the legacy support in Kerberos when Active Directory was released in the year 2000 with Windows Server 2000. This legacy support is enabled when using Kerberos RC4 encryption …
December 2015 archive
Dec 28 2015
Finding Passwords in SYSVOL & Exploiting Group Policy Preferences
At Black Hat and DEF CON this year, I spoke about ways attackers go from Domain User to Domain Admin in modern enterprises. Every Windows computer has a built-in Administrator account with an associated password. Changing this password is a security requirement in most organizations, though the method for doing so is not straight-forward. A …
Dec 14 2015
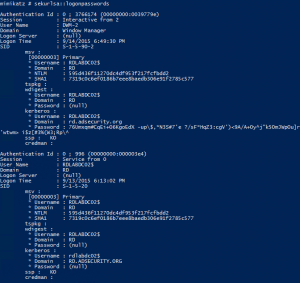
Unofficial Guide to Mimikatz & Command Reference
A new page on ADSecurity.org just went live which is an “unofficial” guide to Mimikatz which also contains an expansive command reference of all available Mimikatz commands. Screenshots, descriptions, and parameters are included where available and appropriate. This page includes the following topics: Mimikatz Overview Mimikatz & Credentials Available Credentials by OS PowerShell & Mimikatz …


Recent Comments