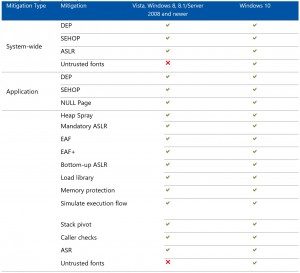
Microsoft recently released Enhanced Mitigation Experience Toolkit (EMET) version 5.5 (it jumped from 5.2 to 5.5) which includes Windows 10 compatibility and better GPO support (among others). I’ve included information from a variety of Microsoft sources in this post so that others don’t have to search for the data separately. The resources/references are listed at …
January 2016 archive
Jan 27 2016
Active Directory Recon Without Admin Rights
A fact that is often forgotten (or misunderstood), is that most objects and their attributes can be viewed (read) by authenticated users (most often, domain users). The challenge is that admins may think that since this data is most easily accessible via admin tools such as “Active Directory User and Computers” (dsa.msc) or “Active Directory …
Jan 22 2016
ADSecurity.org in the Press!
IT World Canada reached out to me recently to help with an article on Active Directory attack & defense. Read the article: “IT not doing enough to secure Active Directory, says expert.” IIT World Canada also requested comments for a second story titled: “22 tips for preventing ransomware attacks“.
Jan 18 2016
So You Want to Speak at a Security Conference?
After performing research at the end of 2014 on Microsoft enterprise security, specifically Active Directory, I realized that others may be interested in this information – my customers certainly were! So, I decided to submit a talk to the various security conferences and see what happened. I certainly didn’t expect to be accepted at 5 …
Jan 05 2016
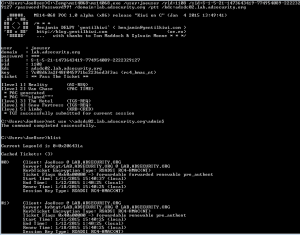
Mimikatz Update Fixes Forged Kerberos Ticket Domain Field Anomaly – Golden Ticket Invalid Domain Field Event Detection No Longer Works
In late 2014, I discovered that the domain field in many events in the Windows security event log are not properly populated when forged Kerberos tickets are used. The key indicator is that the domain field is blank or contains the FQDN instead of the short (netbios) name and depending on the tool used to …
Jan 03 2016
How Attackers Dump Active Directory Database Credentials
I previously posted some information on dumping AD database credentials before in a couple of posts: “How Attackers Pull the Active Directory Database (NTDS.dit) from a Domain Controller” and “Attack Methods for Gaining Domain Admin Rights in Active Directory“. This post covers many different ways that an attacker can dump credentials from Active Directory, both …
Jan 01 2016
Attack Methods for Gaining Domain Admin Rights in Active Directory
There are many ways an attacker can gain Domain Admin rights in Active Directory. This post is meant to describe some of the more popular ones in current use. The techniques described here “assume breach” where an attacker already has a foothold on an internal system and has gained domain user credentials (aka post-exploitation). The …



Recent Comments