Chinese hackers, aka “Deep Panda”, leverage PowerShell while compromising US think-tank computer systems. Recently, we detected breaches of these networks via the use of powershell scripts deployed by the adversary as scheduled tasks on Windows machines. The scripts are passed to the powershell interpreter through the command line to avoid placement of extraneous files on …
Category: Network/System Security
Aug 27 2014
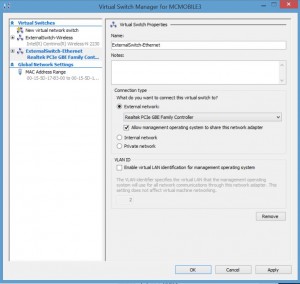
Installing Kali Linux on Windows 8 Hyper-V
Installing Kali Linux on Windows 8 Hyper-V (Windows 8.1 includes improvements to the Hyper-V platform) Installing Hyper-V: Requirement: Windows 8 Pro or Windows 8 Enterprise which include Client Hyper-V. Requirement: Your computer processor must support virtualization technology (VT), though most processors in the past 5 years support VT (pretty much all Intel i-series processors, i3, …
Aug 26 2014
Black Hat 2014 Talk on TSA System Insecurity: Pulling the Curtain on Airport Security
Billy Rios explains how security-focused agencies keep making the same mistakes – this time it’s the TSA. Some of the issues identified in the talk: Network cable connections easily accessible by the public Hardcoded passwords in body scanner systems (which run Windows 98/WinXP) Accounts are stored in a config file. Network services enabled.(with hardcoded passwords) …
Jul 11 2014
Real-Time World Hack Map
This is an incredible map of the world that shows real-time network attacks. The animation makes it look like something out of the movie, “WarGames.” Most impressive. http://map.ipviking.com/?_ga=1.106938115.1477390587.1388686673#

Recent Comments