IT World Canada reached out to me recently to help with an article on Active Directory attack & defense. Read the article: “IT not doing enough to secure Active Directory, says expert.” IIT World Canada also requested comments for a second story titled: “22 tips for preventing ransomware attacks“.
Tag: ADSecurity
Jan 05 2016
Mimikatz Update Fixes Forged Kerberos Ticket Domain Field Anomaly – Golden Ticket Invalid Domain Field Event Detection No Longer Works
In late 2014, I discovered that the domain field in many events in the Windows security event log are not properly populated when forged Kerberos tickets are used. The key indicator is that the domain field is blank or contains the FQDN instead of the short (netbios) name and depending on the tool used to …
Sep 10 2015
DerbyCon V (2015): Red vs. Blue: Modern Active Directory Attacks & Defense Talk Detail
In a couple of weeks, I will be speaking at DerbyCon about Active Directory attack & defense in my talk Red vs. Blue: Modern Active Directory Attacks & Defense”. This is the 5th iteration of this talk and includes the latest updates to attack methods and defensive strategies. This DerbyCon version is a blend of …
Sep 10 2015
Sneaky Active Directory Persistence #11: Directory Service Restore Mode (DSRM)
The content in this post describes a method by which an attacker could persist administrative access to Active Directory after having Domain Admin level rights for 5 minutes. I presented on this AD persistence method in Las Vegas at DEF CON 23 (2015). Complete list of Sneaky Active Directory Persistence Tricks posts The Directory …
May 25 2015
Summer Speaking Engagements
I am thrilled to announce I will be speaking about Active Directory security at the following security conferences: Shakacon (Waikiki Beach, HI) Black Hat USA (Las Vegas, NV) DEF CON (Las Vegas, NV) Each talk will cover current AD attack techniques and the latest defensive methods. Additionally, I will be sharing some exciting new information …
May 03 2015
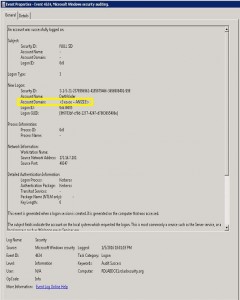
Detecting Forged Kerberos Ticket (Golden Ticket & Silver Ticket) Use in Active Directory
Over the last 6 months, I have been researching forged Kerberos tickets, specifically Golden Tickets, Silver Tickets, and TGTs generated by MS14-068 exploit code (a type of Golden Ticket). I generated forged Kerberos tickets using Mimikatz (Mimikatz Command Reference) and MS14-068 exploits and logged the results. Over the course of several weeks, I identified anomalies …
Sep 15 2014
Active Directory Pentest Recon Part 1: SPN Scanning aka Mining Kerberos Service Principal Names
I wrote a lengthy post on Kerberos earlier which describes the Kerberos protocol as well as how Active Directory leverages Kerberos. There are several interesting Active Directory components useful to the pentester. The one I cover here relates to how Kerberos works, specifically Service Principal Names. As I mentioned in my Kerberos post, Service Principal Names …
Feb 23 2014
Security Considerations for Active Directory (AD) Trusts
TechNet has an article on the Security Considerations for Active Directory (AD) Trusts. This is a must read to fully understand the issues with the security implications of trust configurations. Potential Threats to Interforest Trusts Security Settings for Interforest Trusts Minimum Administrative Credentials for Securing Trusts Trust Security and Other Windows Technologies Related Information …


Recent Comments