In Active Directory, there has been a method that’s been around for many years which changes the password last set date but not the actual password. This is what I call a “fake password change” since the account appears to have a recent password when scanning for old passwords based on password last set, but …
Category: PowerShell
Jan 20 2026
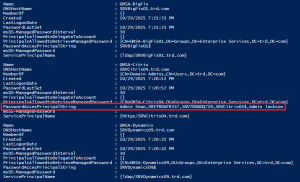
Active Directory Security Tip #16: Mitigating Kerberoast Attacks
There are two main password attacks leveraged by adversaries; one is called Password Spraying and the other is called Kerberoasting. This post focuses on identifying accounts that may be targeted for Kerberoasting and how to harden the environment against Kerberoasting.
Nov 04 2025
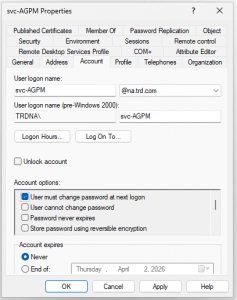
Active Directory Security Tip #14: Group Managed Service Accounts (GMSAs)
Group Managed Service Accounts (GMSAs) User accounts created to be used as service accounts rarely have their password changed. Group Managed Service Accounts (GMSAs) provide a better approach (starting in the Windows 2012 timeframe). The password is managed by AD and automatically changed. This means that the GMSA has to have security principals explicitly delegated …
Oct 08 2025
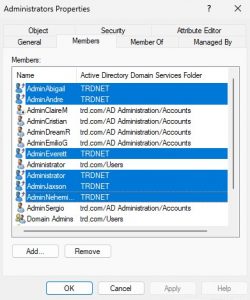
Active Directory Security Tip #13: Reviewing Foreign Security Principals (FSPs)
Review the membership of groups for accounts and groups from another Active Directory forest (technically another domain, but using forest here). These are called “Foreign Security Principals” (FSPs) like the ones highlighted in the image. These FSPs are accounts that exist in another forest but have rights in the AD forest. Any FSPs should be …
Oct 06 2025
Active Directory Security Tip #12: Kerberos Delegation
I have mentioned in several presentations that Kerberos delegation is impersonation. Kerberos delegation is used when a service (ex. web server) needs to impersonate a user when connecting to a resource (ex. database). There are a 4 types of Kerberos delegation: Unconstrained delegation should be converted to constrained delegation due to security concerns. Any Kerberos …
Oct 03 2025
Active Directory Security Tip #11: Print Service on Domain Controllers
The Print Spooler service is a default service on Windows Servers and is set to run at startup. There are a number of attacks that are enabled by having the Print Spooler service running on Domain Controllers (ex.: Printer Bug: https://adsecurity.org/?p=4056) At this point it’s best to configure a GPO to disable the Print Spooler …
Oct 01 2025
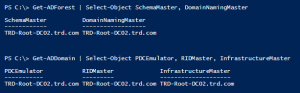
Active Directory Security Tip #10: FSMO Roles
Getting Microsoft supported backups of Domain Controllers is an important part of recovery strategy. A best practice is to locate all Flexible Master Single Operator (FSMO) roles on a single DC in the domain. That way you can more easily target the DC that hosts the FSMOs for backup. PowerShell code to check for FSMO …
Sep 29 2025
Active Directory Security Tip #9: Active Directory Backups
Microsoft supported backups of Active Directory are very important to have. For backing up Domain Controllers, this is typically a System State backup. Why a Microsoft supported backup? If you are using a backup solution that isn’t fully AD aware, performing a restore may involve getting Microsoft involved and that costs $$. I know companies …
Sep 20 2025
Active Directory Security Tip #8: The Domain Kerberos Service Account – KRBTGT
The domain Kerberos service account, KRBTGT (https://adsecurity.org/?p=483), is an important account since it is used to sign & encrypt Kerberos tickets. The account is disabled and the password doesn’t change except when moving from Windows 2000/2003 to Windows Server 2008 (or newer). This is a highly privileged account and if an attacker can gain knowledge …



Recent Comments