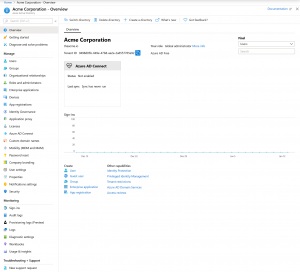
Many are familiar with Active Directory, the on-premises directory and authentication system that is available with Windows Server, but exactly what is Azure Active Directory? Azure Active Directory (Azure AD or AAD) is a multi-tenant cloud directory and authentication service. Azure AD is the directory service that Office 365 (and Azure) leverages for account, groups, …
Tag: AD
Jan 12 2020
What is Azure Active Directory?
- AAD, AccountTokenTheft, ActiveDirectory, ActiveSync, AD, ADAL, ADALPowerShell, AttackingMicrosoftCloud, AttackingOffice365, Azure AD Account Enumeration, AzureActiveDirectory, AzureAD, AzureADPasswordSpray, AzureADPowerShellModule, AzurePIM, CloudAD, ExchangeOnlineModule, GlobalAdmin, GlobalReader, MicrosoftCloud, MicrosoftCloudSecurity, MSOnline, O365, O365Creeper, O365PasswordSpray, Office365, Office365PasswordSpray, Office365security, OWA, PasswordSprayDetection, PasswordSpraying, PIM, PrivilegedIdentityManagement, WhatIsAzureActiveDirectory, WhatIsAzureAD
Jun 14 2017
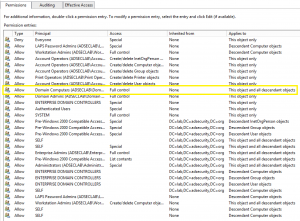
Scanning for Active Directory Privileges & Privileged Accounts
Active Directory Recon is the new hotness since attackers, Red Teamers, and penetration testers have realized that control of Active Directory provides power over the organization. I covered ways to enumerate permissions in AD using PowerView (written by Will @harmj0y) during my Black Hat & DEF CON talks in 2016 from both a Blue Team …
- Account Operators, Active Directory permissions, Active Directory PRivileged Access, Active Directory Security, AD, AD ACLs, AD Delegation, AD groups in Local Groups, AD Security, AdminSDHolder, Allow logon locally, Allow logon over Remote Desktop Services, Backup Operators, Bloodhound, Create GPO rights, CreateChild, DCSync, DeleteChild, Domain Admins, Enable computer and user accounts to be trusted for delegation, Enterprise Admins, Extended Right, Full Control, GenericAll, GenericWrite, GPO, Greoup Policy Delegation, Group Membership, Group Policy Object, Group Policy Permission, Impersonate a client after authentication, Link GPO rights, Manage auditing and security log, Manage Group Policy link, PowerView, Print Operators, Replicating Directory Changes All, Restricted Groups, S-1-5--512, S-1-5--517, S-1-5--520, S-1-5-21--1102, S-1-5-21--519, S-1-5-21--525, S-1-5-21--571, S-1-5-32--574, S-1-5-32-544, S-1-5-32-548, S-1-5-32-550, S-1-5-32-551, S-1-5-32-554, S-1-5-32-562, S-1-5-32-573, S-1-5-32-578, SACL, Schema Admins, SDDL, SDProp, Self, SeMachineAccountPrivilege, SeNetworkLogonRight, SeTcbPrivilege, SeTrustedCredManAccessPrivilege, SIDHistory, Synchronize directory service data, User Rights Assignments, Validated Write, WriteDACL, WriteOwner, WritePRoperty
Aug 15 2016
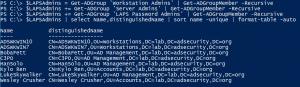
Microsoft LAPS Security & Active Directory LAPS Configuration Recon
Over the years, there have been several methods attempted for managing local Administrator accounts: Scripted password change – Don’t do this. The password is exposed in SYSVOL. Group Policy Preferences. The credentials are exposed in SYSVOL. Password vault/safe product (Thycotic, CyberArk, Lieberman, Quest, Exceedium, etc). Microsoft Local Administrator Password Solution (LAPS). LAPS Overview Microsoft’s …
- Active Directory LAPS, AD, admpwd.dll, Change Local Administrator Password, Find-AdmPwdExtendedRights, HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\GPExtensions, LAPS, LAPS Recon, Local Admin password management, Local Administrator Password Solution, Microsoft LAPS, ms-Mcs-AdmPwd, ms-Mcs-AdmPwdExpirationTime, PowerView
- 2 comments
Recent Posts
- Detecting Fake Active Directory Password Changes
- Active Directory Security Tip #16: Mitigating Kerberoast Attacks
- Active Directory Security Tip #15: Active Directory Domain Root Permissions
- Active Directory Security Tip #14: Group Managed Service Accounts (GMSAs)
- Improve Entra ID Security More Quickly
Active Directory & Entra ID Security Services
Popular Posts
- AD Reading: Windows Server 2019 Active Directory Features
- PowerShell Encoding & Decoding (Base64)
- Attack Methods for Gaining Domain Admin Rights in…
- Kerberos & KRBTGT: Active Directory’s…
- Finding Passwords in SYSVOL & Exploiting Group…
- Securing Windows Workstations: Developing a Secure Baseline
- Securing Domain Controllers to Improve Active…
- Detecting Kerberoasting Activity
- Mimikatz DCSync Usage, Exploitation, and Detection
- Scanning for Active Directory Privileges &…
Categories
- ActiveDirectorySecurity
- Apple Security
- Cloud Security
- Continuing Education
- Entertainment
- Entra ID Security
- Exploit
- Hacking
- Hardware Security
- Hypervisor Security
- Interview
- Linux/Unix Security
- Malware
- Microsoft Security
- Mitigation
- Network/System Security
- PowerShell
- RealWorld
- Security
- Security Conference Presentation/Video
- Security Recommendation
- Technical Article
- Technical Reading
- Technical Reference
- TheCloud
- Vulnerability
Tags
Recent Posts
- Detecting Fake Active Directory Password Changes
- Active Directory Security Tip #16: Mitigating Kerberoast Attacks
- Active Directory Security Tip #15: Active Directory Domain Root Permissions
- Active Directory Security Tip #14: Group Managed Service Accounts (GMSAs)
- Improve Entra ID Security More Quickly
Archives
- March 2026
- January 2026
- December 2025
- November 2025
- October 2025
- September 2025
- August 2025
- December 2020
- May 2020
- January 2020
- August 2019
- March 2019
- February 2019
- October 2018
- August 2018
- May 2018
- January 2018
- November 2017
- August 2017
- June 2017
- May 2017
- February 2017
- January 2017
- November 2016
- October 2016
- September 2016
- August 2016
- July 2016
- June 2016
- April 2016
- March 2016
- February 2016
- January 2016
- December 2015
- November 2015
- October 2015
- September 2015
- August 2015
- July 2015
- June 2015
- May 2015
- April 2015
- March 2015
- February 2015
- January 2015
- December 2014
- November 2014
- October 2014
- September 2014
- August 2014
- July 2014
- June 2014
- May 2014
- April 2014
- March 2014
- February 2014
- July 2013
- November 2012
- March 2012
- February 2012
Categories
- ActiveDirectorySecurity
- Apple Security
- Cloud Security
- Continuing Education
- Entertainment
- Entra ID Security
- Exploit
- Hacking
- Hardware Security
- Hypervisor Security
- Interview
- Linux/Unix Security
- Malware
- Microsoft Security
- Mitigation
- Network/System Security
- PowerShell
- RealWorld
- Security
- Security Conference Presentation/Video
- Security Recommendation
- Technical Article
- Technical Reading
- Technical Reference
- TheCloud
- Vulnerability

Recent Comments