Securing workstations against modern threats is challenging. It seems like every week there’s some new method attackers are using to compromise a system and user credentials. Post updated on March 8th, 2018 with recommended event IDs to audit. The best way to create a secure Windows workstation is to download the Microsoft Security Compliance Manager …
Category: Microsoft Security
Oct 18 2016
BSides DC (2016) Talk – PowerShell Security: Defending the Enterprise from the Latest Attack Platform
This Saturday at BSides DC, I am presenting on the current state of PowerShell security in a talk called, “PowerShell Security: Defending the Enterprise from the Latest Attack Platform.” I cover some of the information I’ve posted here before: PowerShell Version 5 Security Enhancements PowerShell Security: PowerShell Attack Tools, Mitigation, & Detection Detecting Offensive PowerShell …
Sep 13 2016
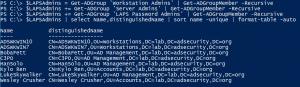
DerbyCon 6 (2016) Talk – Attacking EvilCorp: Anatomy of a Corporate Hack
Next week at DerbyCon 6, Will Schroeder (aka Will Harmjoy, @Harmj0y) & I are presenting on enterprise security, “Attacking EvilCorp: Anatomy of a Corporate Hack.” We call this one the “How You Got Hacked” presentation. The company and events are fictional. The techniques are real. On Saturday, September 24th, 2016, Will & I are speaking …
Aug 15 2016
Microsoft LAPS Security & Active Directory LAPS Configuration Recon
Over the years, there have been several methods attempted for managing local Administrator accounts: Scripted password change – Don’t do this. The password is exposed in SYSVOL. Group Policy Preferences. The credentials are exposed in SYSVOL. Password vault/safe product (Thycotic, CyberArk, Lieberman, Quest, Exceedium, etc). Microsoft Local Administrator Password Solution (LAPS). LAPS Overview Microsoft’s …
Aug 13 2016
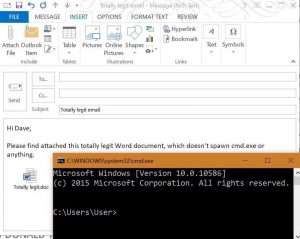
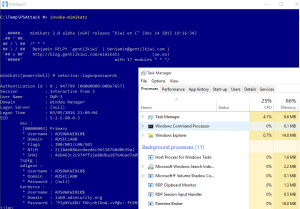
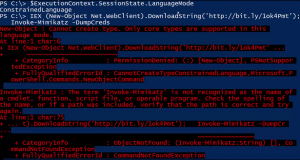
PowerShell Security: PowerShell Attack Tools, Mitigation, & Detection
This post is a follow-up of sorts from my earlier posts on PowerShell, my PowerShell presentation at BSides Baltimore, and my presentation at DEF CON 24. Hopefully this post provides current information on PowerShell usage for both Blue and Red teams. Related posts: BSides Charm Presentation Posted: PowerShell Security: Defending the Enterprise from the Latest …
Jul 06 2016
DEF CON 24 (2016) Talk – Beyond the MCSE: Red Teaming Active Directory
This August at DEF CON 24, I will be speaking about Active Directory security evaluation in my talk “Beyond the MCSE: Red Teaming Active Directory”. This talk is focused on the Red side of AD security, specifically how to best evaluate the security of AD and quickly identify potential security issues. Whether you perform “Red …
Apr 24 2016
BSides Charm Presentation Posted: PowerShell Security: Defending the Enterprise from the Latest Attack Platform
This was my second year speaking at BSides Charm in Baltimore. Last year I spoke about Active Directory attack & defense and it was my first time speaking at a conference. 🙂 The presentation slides for my talk “PowerShell Security: Defending the Enterprise from the Latest Attack Platform” are now on the Presentations tab here …

Recent Comments