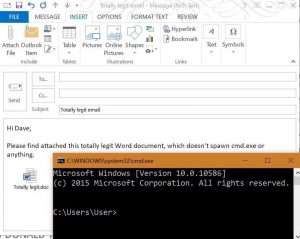
Securing workstations against modern threats is challenging. It seems like every week there’s some new method attackers are using to compromise a system and user credentials. Post updated on March 8th, 2018 with recommended event IDs to audit. The best way to create a secure Windows workstation is to download the Microsoft Security Compliance Manager …
Tag: Disable Windows Scripting Host (WSH)
Oct 21 2016
Securing Windows Workstations: Developing a Secure Baseline
- AppLocker, block macros, Block macros from running in Office files from the Internet, cmd, Control Local Administrator Account, Control Macros, DHCP option 43 hex 0104.0000.0002, Direct hosting of SMB over TCP/IP, Disable LLMNR, Disable NetBIOS, Disable NetSession Enumeration, Disable PowerShell version 2, Disable SMB 1, Disable Windows Scripting Host (WSH), Disable WPAD, EMET, Group Policy, jscript, KB2871997, KB3177451, Lanman Authentication, LAPS, LLMNR, Microsoft Office Macro Security, Microsoft Office Macros, mimikatz, NetCease, NTLM session security, Office 2013 macro, Office 2016 macro security, Office OLE, OLE, packager.dll, port 445, Responder, RID 500, Secure Windows Workstation, Server Message Block, SMB, Telemetry Dashboard, VBA, VBScript, WDigest, Windows 10 build image, WPAD, wscript
- 5 comments
Recent Posts
- Detecting Fake Active Directory Password Changes
- Active Directory Security Tip #16: Mitigating Kerberoast Attacks
- Active Directory Security Tip #15: Active Directory Domain Root Permissions
- Active Directory Security Tip #14: Group Managed Service Accounts (GMSAs)
- Improve Entra ID Security More Quickly
Active Directory & Entra ID Security Services
Have concerns about your Active Directory environment and/or Entra ID tenant?
We help enterprises improve their security posture.
Popular Posts
- AD Reading: Windows Server 2019 Active Directory Features
- PowerShell Encoding & Decoding (Base64)
- Attack Methods for Gaining Domain Admin Rights in…
- Kerberos & KRBTGT: Active Directory’s…
- Finding Passwords in SYSVOL & Exploiting Group…
- Securing Windows Workstations: Developing a Secure Baseline
- Securing Domain Controllers to Improve Active…
- Detecting Kerberoasting Activity
- Mimikatz DCSync Usage, Exploitation, and Detection
- Scanning for Active Directory Privileges &…
Categories
- ActiveDirectorySecurity
- Apple Security
- Cloud Security
- Continuing Education
- Entertainment
- Entra ID Security
- Exploit
- Hacking
- Hardware Security
- Hypervisor Security
- Interview
- Linux/Unix Security
- Malware
- Microsoft Security
- Mitigation
- Network/System Security
- PowerShell
- RealWorld
- Security
- Security Conference Presentation/Video
- Security Recommendation
- Technical Article
- Technical Reading
- Technical Reference
- TheCloud
- Vulnerability
Tags
ActiveDirectory
Active Directory
ActiveDirectorySecurity
Active Directory Security
ActiveDirectorySecurityTip
ADReading
ADSecurity
AD Security
Azure
DCSync
DomainController
GoldenTicket
HyperV
Invoke-Mimikatz
KB3011780
KDC
Kerberoast
Kerberos
KerberosHacking
KRBTGT
LAPS
LSASS
MCM
MicrosoftEMET
MicrosoftWindows
mimikatz
MS14068
PassTheHash
PowerShell
PowerShellCode
PowerShellHacking
PowerShellv5
PowerSploit
PowerView
Presentation
Security
SilverTicket
SneakyADPersistence
SPN
TGS
TGT
Windows10
WindowsServer2008R2
WindowsServer2012
WindowsServer2012R2
Recent Posts
- Detecting Fake Active Directory Password Changes
- Active Directory Security Tip #16: Mitigating Kerberoast Attacks
- Active Directory Security Tip #15: Active Directory Domain Root Permissions
- Active Directory Security Tip #14: Group Managed Service Accounts (GMSAs)
- Improve Entra ID Security More Quickly
Archives
- March 2026
- January 2026
- December 2025
- November 2025
- October 2025
- September 2025
- August 2025
- December 2020
- May 2020
- January 2020
- August 2019
- March 2019
- February 2019
- October 2018
- August 2018
- May 2018
- January 2018
- November 2017
- August 2017
- June 2017
- May 2017
- February 2017
- January 2017
- November 2016
- October 2016
- September 2016
- August 2016
- July 2016
- June 2016
- April 2016
- March 2016
- February 2016
- January 2016
- December 2015
- November 2015
- October 2015
- September 2015
- August 2015
- July 2015
- June 2015
- May 2015
- April 2015
- March 2015
- February 2015
- January 2015
- December 2014
- November 2014
- October 2014
- September 2014
- August 2014
- July 2014
- June 2014
- May 2014
- April 2014
- March 2014
- February 2014
- July 2013
- November 2012
- March 2012
- February 2012
Categories
- ActiveDirectorySecurity
- Apple Security
- Cloud Security
- Continuing Education
- Entertainment
- Entra ID Security
- Exploit
- Hacking
- Hardware Security
- Hypervisor Security
- Interview
- Linux/Unix Security
- Malware
- Microsoft Security
- Mitigation
- Network/System Security
- PowerShell
- RealWorld
- Security
- Security Conference Presentation/Video
- Security Recommendation
- Technical Article
- Technical Reading
- Technical Reference
- TheCloud
- Vulnerability

Recent Comments