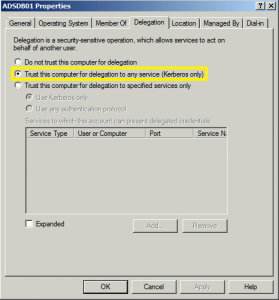
At Black Hat USA 2015 this summer (2015), I spoke about the danger in having Kerberos Unconstrained Delegation configured in the environment. When Active Directory was first released with Windows 2000 Server, Microsoft had to provide a simple mechanism to support scenarios where a user authenticates to a Web Server via Kerberos and needs to …
Category: Microsoft Security
Aug 07 2015
Kerberos Golden Tickets are Now More Golden
At my talk at Black Hat USA 2015, I highlighted new Golden Ticket capability in Mimikatz (“Enhanced Golden Tickets”). This post provides additional detailed on “enhanced” Golden Tickets. Over the past few months, I researched how SID History can be abused in modern enterprises. As part of this research, I reached out to Benjamin Delpy, …
Aug 02 2015
DEF CON 23 (2015) Red vs Blue: Modern Active Directory Attacks & Defense Talk Detail
This week at DEF CON 23, I will be speaking about Active Directory attack & defense in my talk “Red vs Blue: Modern Active Directory Attacks & Defense”. This is the 4th iteration of this talk and includes the latest updates to attack methods and defensive strategies.This DEF CON version has a new segment I …
Jul 26 2015
Black Hat USA 2015 Red vs Blue Active Directory Attack & Defense Talk Detail
Next week at Black Hat USA 2015, I will be speaking about Active Directory attack & defense in my talk “Red vs Blue: Modern Active Directory Attacks Detection and Protection”. This is the 3rd iteration of this talk and includes the latest updates to attack methods and defensive strategies. I’m including lots of updates and …
Jul 15 2015
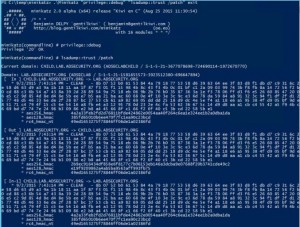
It’s All About Trust – Forging Kerberos Trust Tickets to Spoof Access across Active Directory Trusts
In early 2015, I theorized that it’s possible to forge inter-realm (inter-trust) Kerberos tickets in a similar manner to how intra-domain TGTs (Golden Tickets) and TGSs (Silver Tickets) are forged. Around the same time, Benjamin Delpy updated Mimikatz to dump trust keys from a Domain Controller. Soon after, Mimikatz gained capability to forge inter-realm trust …
Jun 24 2015
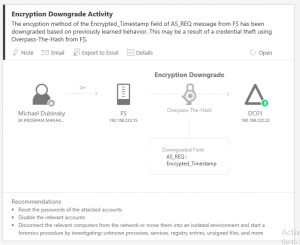
Microsoft Advanced Threat Analytics (ATA) Overview
Introduction There are several methods for identifying unusual or anomalous user activity. Traditionally these methods have required certain events be logged to the Windows event logs on workstations, servers, and Domain Controllers (DCs) and these events need to be forwarded to a central collection system. The drawback to this approach is numerous: the data logged …
May 25 2015
Summer Speaking Engagements
I am thrilled to announce I will be speaking about Active Directory security at the following security conferences: Shakacon (Waikiki Beach, HI) Black Hat USA (Las Vegas, NV) DEF CON (Las Vegas, NV) Each talk will cover current AD attack techniques and the latest defensive methods. Additionally, I will be sharing some exciting new information …
May 11 2015
Detecting Mimikatz Use
Benjamin Delpy published some YARA rules in detecting Mimikatz use in your environment. More information on Mimikatz capability is in the “Unofficial Mimikatz Guide & Command Reference” on this site. YARA is described as: YARA is a tool aimed at (but not limited to) helping malware researchers to identify and classify malware samples. With YARA …
May 08 2015
Microsoft Ignite 2015 Security Sessions
Microsoft retired several conferences this year (TechEd, MEC, MMC, etc) and merged them into a single mega-conference called Microsoft Ignite 2015. About 23,000 people (~29k including all staff and support personnel) converged on the McCormick Place Conference Center in Chicago, IL during the week of May 4th (May the Fourth be With You!). I recently …


Recent Comments