The content in this post describes a method by which an attacker could persist administrative access to Active Directory after having Domain Admin level rights for about 5 minutes. All posts in my Sneaky Active Directory Persistence Tricks series This post explores how an attacker could leverage computer account credentials to persist in an enterprise …
19 results for DCSync
Feb 11 2016
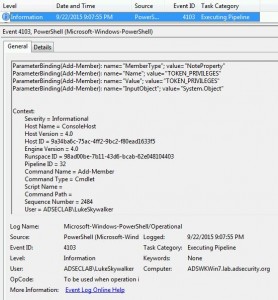
Detecting Offensive PowerShell Attack Tools
At DerbyCon V (2015), I presented on Active Directory Attack & Defense and part of this included how to detect & defend against PowerShell attacks. Update: I presented at BSides Charm (Baltimore) on PowerShell attack & defense in April 2016. More information on PowerShell Security: PowerShell Security: PowerShell Attack Tools, Mitigation, & Detection The most …
Top Posts
ADSecurity.org Active Directory Security Top Posts: Attack Methods for Gaining Domain Admin Rights in Active Directory Mimikatz Guide and Command Reference Microsoft Local Administrator Password Solution (LAPS) How Attackers Dump Active Directory Database Credentials Active Directory Recon Without Admin Rights The Most Common Active Directory Security Issues and What You Can Do to Fix Them …
Jan 03 2016
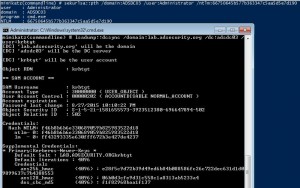
How Attackers Dump Active Directory Database Credentials
I previously posted some information on dumping AD database credentials before in a couple of posts: “How Attackers Pull the Active Directory Database (NTDS.dit) from a Domain Controller” and “Attack Methods for Gaining Domain Admin Rights in Active Directory“. This post covers many different ways that an attacker can dump credentials from Active Directory, both …
Nov 30 2015
Real-World Example of How Active Directory Can Be Compromised (RSA Conference Presentation)
At the RSA Conference in Abu Dhabi earlier this month, Stefano Maccaglia (Incident Response Consultant with RSA) presented “Evolving Threats: dissection of a Cyber-Espionage attack.” The slides for this talk are available on the RSA Conference site (UPDATE: RSA removed the slides from their site, Presentation Slides on Yumpu). This post covers and adds some …
Nov 17 2015
How Attackers Use Kerberos Silver Tickets to Exploit Systems
Usually Golden Tickets (forged Kerberos TGTs) get all the press, but this post is about Silver Tickets and how attackers use them to exploit systems. I have talked about how Silver Tickets can be used to persist and even re-exploit an Active Directory enterprise in presentations at security conferences this year. This post continues this …
Sep 25 2015
Sneaky Active Directory Persistence #13: DSRM Persistence v2
The content in this post describes a method by which an attacker could persist administrative access to Active Directory after having Domain Admin level rights for 5 minutes. I presented on this AD persistence method at DerbyCon (2015). I also presented and posted on DSRM as a persistence method previously. Complete list of Sneaky Active …
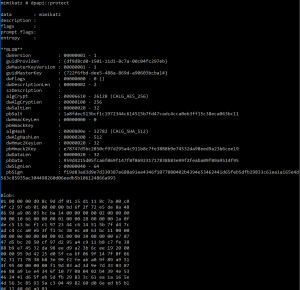
Mimikatz
Unofficial Guide to Mimikatz & Command Reference Mimikatz Command Reference Version: mimikatz 2.1.1 (x64) built on Nov 28 2017 Page last updated: February 17th, 2018 Introduction: It seems like many people on both sides of the fence, Red & Blue, aren’t familiar with most of Mimikatz’s capabilities, so I put together this information on all …
Security Resources
This page is a reference with security documents, posts, videos and presentations I find useful for staying up to date on current security issues and exploits. Last Updated: May 2016 Note that this page isn’t actively updated. Visit the Attack, Defense, & Detection page for updated content. Microsoft Enterprise & Active Directory Security Documents (& Blog …
- 1
- 2




Recent Comments