ADSecurity.org Active Directory Security Top Posts: Attack Methods for Gaining Domain Admin Rights in Active Directory Mimikatz Guide and Command Reference Microsoft Local Administrator Password Solution (LAPS) How Attackers Dump Active Directory Database Credentials Active Directory Recon Without Admin Rights The Most Common Active Directory Security Issues and What You Can Do to Fix Them …
22 results for LAPS
Jan 01 2016
Attack Methods for Gaining Domain Admin Rights in Active Directory
There are many ways an attacker can gain Domain Admin rights in Active Directory. This post is meant to describe some of the more popular ones in current use. The techniques described here “assume breach” where an attacker already has a foothold on an internal system and has gained domain user credentials (aka post-exploitation). The …
Dec 28 2015
Finding Passwords in SYSVOL & Exploiting Group Policy Preferences
At Black Hat and DEF CON this year, I spoke about ways attackers go from Domain User to Domain Admin in modern enterprises. Every Windows computer has a built-in Administrator account with an associated password. Changing this password is a security requirement in most organizations, though the method for doing so is not straight-forward. A …
Oct 14 2015
The Most Common Active Directory Security Issues and What You Can Do to Fix Them
The past couple of years of meeting with customers is enlightening since every environment, though unique, often has the same issues. These issues often boil down to legacy management of the enterprise Microsoft platform going back a decade or more. I spoke about Active Directory attack and defense at several security conferences this year including …
Sep 25 2015
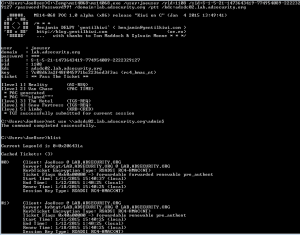
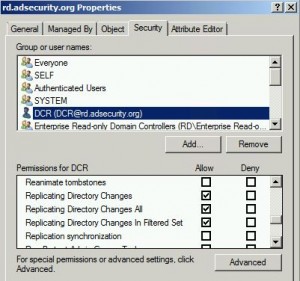
Mimikatz DCSync Usage, Exploitation, and Detection
Note: I presented on this AD persistence method at DerbyCon (2015). A major feature added to Mimkatz in August 2015 is “DCSync” which effectively “impersonates” a Domain Controller and requests account password data from the targeted Domain Controller. DCSync was written by Benjamin Delpy and Vincent Le Toux. The exploit method prior to DCSync was …
Jan 19 2015
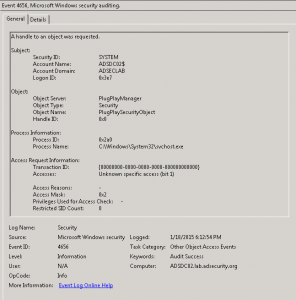
Attackers Can Now Use Mimikatz to Implant Skeleton Key on Domain Controllers & BackDoor Your Active Directory Forest
Once an attacker has gained Domain Admin rights to your Active Directory environment, there are several methods for keeping privileged access. Skeleton Key is an ideal persistence method for the modern attacker. More information on Skeleton Key is in my earlier post. Note that the behavior documented in this post was observed in a lab …
Nov 16 2014
PowerShell 101: Easy Script Timing
There are times when you want to know how long it takes for a script to run. One of the Measure-* cmdlets can be useful, but there is a simpler way to time how long it takes to run a script (or piece of code). The StopWatch .NET method is an ideal method for script …
Nov 03 2014
Virtualization Updates to Active Directory 2012
As part of the many updates to Active Directory, one of the most interesting is virtualization safeguarding in Windows Server 2012. Active Directory Domain Controllers running Windows Server 2012 can now identify if they are virtualized and have been improperly restored or cloned (copied). Windows Server 2012 introduces a new feature called the VM Generation …
Security Resources
This page is a reference with security documents, posts, videos and presentations I find useful for staying up to date on current security issues and exploits. Last Updated: May 2016 Note that this page isn’t actively updated. Visit the Attack, Defense, & Detection page for updated content. Microsoft Enterprise & Active Directory Security Documents (& Blog …
SPNs
Active Directory Service Principal Names (SPNs) Descriptions Excellent article describing how Service Principal Names (SPNs) are used by Kerberos and Active Directory: Service Principal Names (SPNs) SetSPN Syntax (Setspn.exe) This page is a comprehensive reference (as comprehensive as possible) for Active Directory Service Principal Names (SPNs). As I discover more SPNs, they will be added. …


Recent Comments