Introduction Kerberoasting can be an effective method for extracting service account credentials from Active Directory as a regular user without sending any packets to the target system. This attack is effective since people tend to create poor passwords. The reason why this attack is successful is that most service account passwords are the same length …
Tag: KerberosRequestorSecurityToken
Feb 05 2017
Detecting Kerberoasting Activity
- AP-REQ, Audit Kerberos Service Ticket Operations, Detect Kerberoast Activity, Detecting Kerberoast activity, Event ID 4769, Kerberoasting Active Directory, Kerberoasting activity, Kerberos RC4 Encryption, Kerberos Service Ticket, Kerberos TGS, Kerberos TGS Ticket, KerberosRequestorSecurityToken, NTLM Password, PowerShell Kerberoast, RC4_HMAC_MD5, TGS-REP, TGS-REQ
Jan 29 2017
Sneaky Persistence Active Directory Trick #18: Dropping SPNs on Admin Accounts for Later Kerberoasting
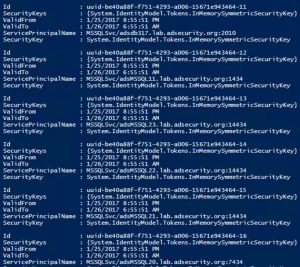
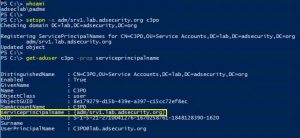
The content in this post describes a method through which an attacker could persist administrative access to Active Directory after having Domain Admin level rights for about 5 minutes. Complete list of Sneaky Active Directory Persistence Tricks posts This post explores how an attacker could leverage existing admin rights and/or over-permissive delegation to gain persistence …
- AD Sneaky Persistence, attacking kerberos, Kerberoast, kerberoasting, Kerberos attack, Kerberos Ticket Cracking, KerberosRequestorSecurityToken, PowerShell Kerberoasting, RC4 TGS ticket, service principal name, sneaky persistence tricks, SPN, System.IdentityModel, TGS cracking, Write ServicePrincipalName
Recent Posts
- Detecting Fake Active Directory Password Changes
- Active Directory Security Tip #16: Mitigating Kerberoast Attacks
- Active Directory Security Tip #15: Active Directory Domain Root Permissions
- Active Directory Security Tip #14: Group Managed Service Accounts (GMSAs)
- Improve Entra ID Security More Quickly
Active Directory & Entra ID Security Services
Have concerns about your Active Directory environment and/or Entra ID tenant?
We help enterprises improve their security posture.
Popular Posts
- AD Reading: Windows Server 2019 Active Directory Features
- PowerShell Encoding & Decoding (Base64)
- Attack Methods for Gaining Domain Admin Rights in…
- Kerberos & KRBTGT: Active Directory’s…
- Finding Passwords in SYSVOL & Exploiting Group…
- Securing Windows Workstations: Developing a Secure Baseline
- Securing Domain Controllers to Improve Active…
- Detecting Kerberoasting Activity
- Mimikatz DCSync Usage, Exploitation, and Detection
- Scanning for Active Directory Privileges &…
Categories
- ActiveDirectorySecurity
- Apple Security
- Cloud Security
- Continuing Education
- Entertainment
- Entra ID Security
- Exploit
- Hacking
- Hardware Security
- Hypervisor Security
- Interview
- Linux/Unix Security
- Malware
- Microsoft Security
- Mitigation
- Network/System Security
- PowerShell
- RealWorld
- Security
- Security Conference Presentation/Video
- Security Recommendation
- Technical Article
- Technical Reading
- Technical Reference
- TheCloud
- Vulnerability
Tags
ActiveDirectory
Active Directory
ActiveDirectorySecurity
Active Directory Security
ActiveDirectorySecurityTip
ADReading
ADSecurity
AD Security
Azure
DCSync
DomainController
GoldenTicket
HyperV
Invoke-Mimikatz
KB3011780
KDC
Kerberoast
Kerberos
KerberosHacking
KRBTGT
LAPS
LSASS
MCM
MicrosoftEMET
MicrosoftWindows
mimikatz
MS14068
PassTheHash
PowerShell
PowerShellCode
PowerShellHacking
PowerShellv5
PowerSploit
PowerView
Presentation
Security
SilverTicket
SneakyADPersistence
SPN
TGS
TGT
Windows10
WindowsServer2008R2
WindowsServer2012
WindowsServer2012R2
Recent Posts
- Detecting Fake Active Directory Password Changes
- Active Directory Security Tip #16: Mitigating Kerberoast Attacks
- Active Directory Security Tip #15: Active Directory Domain Root Permissions
- Active Directory Security Tip #14: Group Managed Service Accounts (GMSAs)
- Improve Entra ID Security More Quickly
Archives
- March 2026
- January 2026
- December 2025
- November 2025
- October 2025
- September 2025
- August 2025
- December 2020
- May 2020
- January 2020
- August 2019
- March 2019
- February 2019
- October 2018
- August 2018
- May 2018
- January 2018
- November 2017
- August 2017
- June 2017
- May 2017
- February 2017
- January 2017
- November 2016
- October 2016
- September 2016
- August 2016
- July 2016
- June 2016
- April 2016
- March 2016
- February 2016
- January 2016
- December 2015
- November 2015
- October 2015
- September 2015
- August 2015
- July 2015
- June 2015
- May 2015
- April 2015
- March 2015
- February 2015
- January 2015
- December 2014
- November 2014
- October 2014
- September 2014
- August 2014
- July 2014
- June 2014
- May 2014
- April 2014
- March 2014
- February 2014
- July 2013
- November 2012
- March 2012
- February 2012
Categories
- ActiveDirectorySecurity
- Apple Security
- Cloud Security
- Continuing Education
- Entertainment
- Entra ID Security
- Exploit
- Hacking
- Hardware Security
- Hypervisor Security
- Interview
- Linux/Unix Security
- Malware
- Microsoft Security
- Mitigation
- Network/System Security
- PowerShell
- RealWorld
- Security
- Security Conference Presentation/Video
- Security Recommendation
- Technical Article
- Technical Reading
- Technical Reference
- TheCloud
- Vulnerability

Recent Comments