The content in this post describes a method through which an attacker could persist administrative access to Active Directory after having Domain Admin level rights for about 5 minutes. Complete list of Sneaky Active Directory Persistence Tricks posts This post explores how an attacker could leverage the built-in Active Directory management capability called Group Policy …
19 results for laps security
Jan 27 2016
Active Directory Recon Without Admin Rights
A fact that is often forgotten (or misunderstood), is that most objects and their attributes can be viewed (read) by authenticated users (most often, domain users). The challenge is that admins may think that since this data is most easily accessible via admin tools such as “Active Directory User and Computers” (dsa.msc) or “Active Directory …
Top Posts
ADSecurity.org Active Directory Security Top Posts: Attack Methods for Gaining Domain Admin Rights in Active Directory Mimikatz Guide and Command Reference Microsoft Local Administrator Password Solution (LAPS) How Attackers Dump Active Directory Database Credentials Active Directory Recon Without Admin Rights The Most Common Active Directory Security Issues and What You Can Do to Fix Them …
Jan 01 2016
Attack Methods for Gaining Domain Admin Rights in Active Directory
There are many ways an attacker can gain Domain Admin rights in Active Directory. This post is meant to describe some of the more popular ones in current use. The techniques described here “assume breach” where an attacker already has a foothold on an internal system and has gained domain user credentials (aka post-exploitation). The …
Dec 28 2015
Finding Passwords in SYSVOL & Exploiting Group Policy Preferences
At Black Hat and DEF CON this year, I spoke about ways attackers go from Domain User to Domain Admin in modern enterprises. Every Windows computer has a built-in Administrator account with an associated password. Changing this password is a security requirement in most organizations, though the method for doing so is not straight-forward. A …
Sep 25 2015
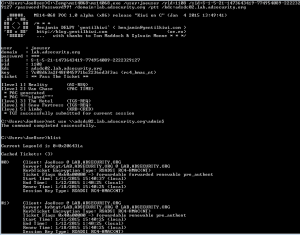
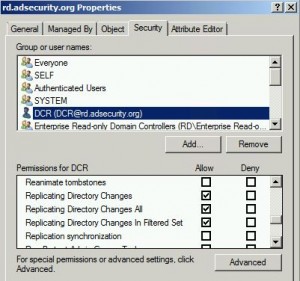
Mimikatz DCSync Usage, Exploitation, and Detection
Note: I presented on this AD persistence method at DerbyCon (2015). A major feature added to Mimkatz in August 2015 is “DCSync” which effectively “impersonates” a Domain Controller and requests account password data from the targeted Domain Controller. DCSync was written by Benjamin Delpy and Vincent Le Toux. The exploit method prior to DCSync was …
Jan 19 2015
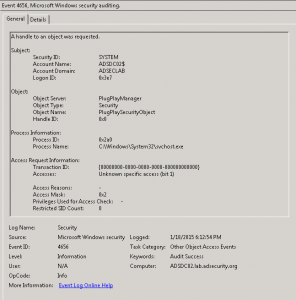
Attackers Can Now Use Mimikatz to Implant Skeleton Key on Domain Controllers & BackDoor Your Active Directory Forest
Once an attacker has gained Domain Admin rights to your Active Directory environment, there are several methods for keeping privileged access. Skeleton Key is an ideal persistence method for the modern attacker. More information on Skeleton Key is in my earlier post. Note that the behavior documented in this post was observed in a lab …
SPNs
Active Directory Service Principal Names (SPNs) Descriptions Excellent article describing how Service Principal Names (SPNs) are used by Kerberos and Active Directory: Service Principal Names (SPNs) SetSPN Syntax (Setspn.exe) This page is a comprehensive reference (as comprehensive as possible) for Active Directory Service Principal Names (SPNs). As I discover more SPNs, they will be added. …
Aug 20 2014
Microsoft EMET 5 Released
Microsoft’s EMET (Enhanced Mitigation Experience Toolkit) is a free download from Microsoft that enhances Windows security by preventing common malware and exploitation software methods. It does need to be well-tested before deployment, but there are several legacy Windows methods leveraged by malware to get into a system and take control. Installing EMET provides very strong protection …
- 1
- 2



Recent Comments