I improve security for enterprises around the world working for TrustedSec & I am @PyroTek3 on Twitter. Read the About page (top left) for information about me. :) https://adsecurity.org/?page_id=8
Author's posts
Oct 03 2025
Active Directory Security Tip #11: Print Service on Domain Controllers
The Print Spooler service is a default service on Windows Servers and is set to run at startup. There are a number of attacks that are enabled by having the Print Spooler service running on Domain Controllers (ex.: Printer Bug: https://adsecurity.org/?p=4056) At this point it’s best to configure a GPO to disable the Print Spooler …
Oct 01 2025
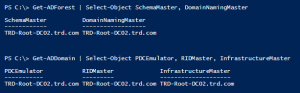
Active Directory Security Tip #10: FSMO Roles
Getting Microsoft supported backups of Domain Controllers is an important part of recovery strategy. A best practice is to locate all Flexible Master Single Operator (FSMO) roles on a single DC in the domain. That way you can more easily target the DC that hosts the FSMOs for backup. PowerShell code to check for FSMO …
Sep 29 2025
Active Directory Security Tip #9: Active Directory Backups
Microsoft supported backups of Active Directory are very important to have. For backing up Domain Controllers, this is typically a System State backup. Why a Microsoft supported backup? If you are using a backup solution that isn’t fully AD aware, performing a restore may involve getting Microsoft involved and that costs $$. I know companies …
Sep 20 2025
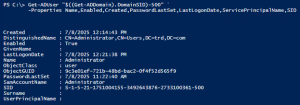
Active Directory Security Tip #8: The Domain Kerberos Service Account – KRBTGT
The domain Kerberos service account, KRBTGT (https://adsecurity.org/?p=483), is an important account since it is used to sign & encrypt Kerberos tickets. The account is disabled and the password doesn’t change except when moving from Windows 2000/2003 to Windows Server 2008 (or newer). This is a highly privileged account and if an attacker can gain knowledge …
Sep 19 2025
Active Directory Security Tip #7: The Tombstone Lifetime
The Tombstone lifetime (TSL) in Active Directory is the limit as to how long a deleted object can remain in AD. The original value was 60 (days). Windows versions since Windows 2003 SP2 have this set to 180 (days). Note that this also affects backups, how long a backup is valid and replication – if …
Sep 16 2025
Active Directory Security Tip #4: Default/Built-In Active Directory Groups
There are several default/built-in privileged groups that should be reviewed: https://learn.microsoft.com/en-us/windows-server/identity/ad-ds/manage/understand-security-groups PowerShell Script leveraging the Active Directory PowerShell module: https://github.com/PyroTek3/ActiveDirectory/blob/main/Get-ADBuiltInAdmins.ps1
Sep 16 2025
Active Directory Lab Build Script
Over the summer, I rebuilt my Active Directory lab environment with multiple regional domains. Instead of manually configuring common issues, I decided to create a PowerShell script to do this for me.




Recent Comments