I improve security for enterprises around the world working for TrustedSec & I am @PyroTek3 on Twitter. Read the About page (top left) for information about me. :) https://adsecurity.org/?page_id=8
Author's posts
Sep 12 2014
Kerberos, Active Directory’s Secret Decoder Ring
Kerberos Overview Kerberos is a protocol with roots in MIT named after the three-headed dog, Cerberus. Named because there are 3 parties: the client, the resource server, and a 3rd party (the Key Distribution Center, KDC). Kerberos can be a difficult authentication protocol to describe, so I will attempt to simplify it as best as …
Sep 10 2014
PowerShell v5 Preview
PowerShell Magazine notes that the September 2014 preview of Windows Management Framework 5.0 (PowerShell v5) is available for download here. Here’s a list of changes as noted in this article by PowerShell Magazine: Some of these changes are: Generate Windows PowerShell cmdlets based on an OData endpoint Manage .ZIP files with new cmdlets DSC Authoring …
Sep 07 2014
Investigating PowerShell Attacks
PowerShell is a compelling method for attackers (and pentesters) since code is run in memory and there is no reason to touch disk (unlike executables, batch files, and vbscripts). Projects like PowerSploit and POSHSec prove that PowerShell is the future of attacks. PowerShell Magazine has a great article on Investigating PowerShell Attacks: Prior articles by …
Sep 06 2014
The Evolution of Protected Processes Part 1: Pass-the-Hash Mitigations in Windows 8.1
Pass-the-Hash has been around for years The post on Alex Ionescu’s blog, The Evolution of Protected Processes Part 1: Pass-the-Hash Mitigations in Windows 8.1, describes the latest mitigation techniques Microsoft is incorporating in the latest versions of Windows. He describes the importance of LSASS in his post: (emphasis/bold text is my own) The LSASS Process In …
Sep 05 2014
Hacking with PowerShell
Chinese hackers, aka “Deep Panda”, leverage PowerShell while compromising US think-tank computer systems. Recently, we detected breaches of these networks via the use of powershell scripts deployed by the adversary as scheduled tasks on Windows machines. The scripts are passed to the powershell interpreter through the command line to avoid placement of extraneous files on …
Sep 03 2014
Machine Account (AD Computer Object) Password Updates
There seems to be quite a bit of confusion when it comes to domain-joined computers and how/when they update their AD computer object (machine account) passwords. Here are a few key points on this process: The default domain policy setting configures domain-joined Windows 2000 (& up) computers to update their passwords every 30 days (default). …
Sep 02 2014
PowerShell: Using Active Directory .Net methods in PowerShell Part 2
Powershell has the incredible ability to run some .Net methods natively. Some of this data can also be gathered using AD commandlets. Read Part 1 for others. Here are a few of my favorites. Get a Computer’s Site: [System.DirectoryServices.ActiveDirectory.ActiveDirectorySite]::GetComputerSite() Get a User’s Domain: [System.DirectoryServices.ActiveDirectory.Domain]::GetCurrentDomain().Name Get a Computer’s Domain: [System.DirectoryServices.ActiveDirectory.Domain]::GetComputerDomain().Name List Active Directory FSMOs: …
Sep 01 2014
PowerShell Parameters
One of the most useful features in Powershell is Parameters. Microsoft has some excellent documentation on Powershell Parameters Some of my favorites: Default Parameter [Switch]$Enabled = $True Mandatory Parameter [parameter(Mandatory=$true)] [String]$Name Validate Parameter Options in a set [ValidateSet(“TCP”, “UDP”)] [string]$NewPortType Validate Parameter Options in a range (case INsensitive) [ValidateRange(1,65535)] [string]$NewPortNumber Add Parameter Aliases [alias(“PortScope”,”Scope”)] [string] …
Aug 30 2014
PowerShell: Drop (remove) the last character from a string
Drop (remove) the last character from a string: $ComputerName = ‘DCCOMP01$’ $ComputerName = $ComputerName.Substring(0,$ComputerName.Length-1) $ComputerName Result is “DCCOMP01″. This works especially well when the last character is a special PowerShell reserved one like “$”.
Aug 27 2014
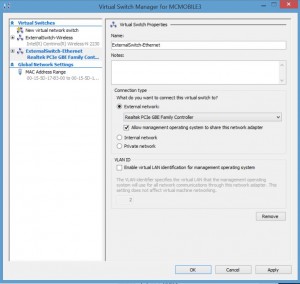
Installing Kali Linux on Windows 8 Hyper-V
Installing Kali Linux on Windows 8 Hyper-V (Windows 8.1 includes improvements to the Hyper-V platform) Installing Hyper-V: Requirement: Windows 8 Pro or Windows 8 Enterprise which include Client Hyper-V. Requirement: Your computer processor must support virtualization technology (VT), though most processors in the past 5 years support VT (pretty much all Intel i-series processors, i3, …

Recent Comments