Microsoft Security Advisory 3010060: Vulnerability in Microsoft OLE Could Allow Remote Code Execution (Published: October 21, 2014) PowerPoint Zero Day Vulnerability Executive Summary: Microsoft is aware of a vulnerability affecting all supported releases of Microsoft Windows, excluding Windows Server 2003. The vulnerability could allow remote code execution if a user opens a specially crafted Microsoft …
Category: Microsoft Security
Oct 06 2014
Comparing ASLR on Windows & Linux
Two key differences regarding Linux & Windows Address Space Layout Randomization (ASLR): ASLR is not as prevalent in most Linux distributions as it is on modern Windows systems. ASLR cannot be force-enabled for applications on Linux, as EMET can do on Windows. Read the entire article at Cert.org
Oct 02 2014
Using PowerShell to Perform a Reverse DNS Lookup in Active Directory
Typically, one would use ping -a to get the hostname for a specific IP address which performs a DNS reverse lookup. Querying AD for a computer with an IP works great for computers joined to the Active Directory domain since most computers in AD have the IP Address configured on the computer account. When the …
Oct 01 2014
Black Hat USA 2014 Presentation: Investigating PowerShell Attacks
Black Hat USA 2014 Presentation: Investigating PowerShell Attacks This is an excellent presentation and I highly recommend anyone who is an admin or who is responsible for AD security. Investigating PowerShell Attacks Ryan Kazanciyan Technical Director, Mandiant Matt Hastings Consultant, Mandiant Over the past two years, we’ve seen targeted attackers increasingly utilize PowerShell to conduct …
Sep 29 2014
Disarming EMET 5
EMET version 5 has been out for only a few months and Offensive Security has identified bypass methods: INTRODUCTION In our previous Disarming Emet 4.x blog post, we demonstrated how to disarm the ROP mitigations introduced in EMET 4.x by abusing a global variable in the .data section located at a static offset. A general …
Sep 15 2014
Active Directory Pentest Recon Part 1: SPN Scanning aka Mining Kerberos Service Principal Names
I wrote a lengthy post on Kerberos earlier which describes the Kerberos protocol as well as how Active Directory leverages Kerberos. There are several interesting Active Directory components useful to the pentester. The one I cover here relates to how Kerberos works, specifically Service Principal Names. As I mentioned in my Kerberos post, Service Principal Names …
Sep 12 2014
Kerberos, Active Directory’s Secret Decoder Ring
Kerberos Overview Kerberos is a protocol with roots in MIT named after the three-headed dog, Cerberus. Named because there are 3 parties: the client, the resource server, and a 3rd party (the Key Distribution Center, KDC). Kerberos can be a difficult authentication protocol to describe, so I will attempt to simplify it as best as …
Sep 07 2014
Investigating PowerShell Attacks
PowerShell is a compelling method for attackers (and pentesters) since code is run in memory and there is no reason to touch disk (unlike executables, batch files, and vbscripts). Projects like PowerSploit and POSHSec prove that PowerShell is the future of attacks. PowerShell Magazine has a great article on Investigating PowerShell Attacks: Prior articles by …
Sep 06 2014
The Evolution of Protected Processes Part 1: Pass-the-Hash Mitigations in Windows 8.1
Pass-the-Hash has been around for years The post on Alex Ionescu’s blog, The Evolution of Protected Processes Part 1: Pass-the-Hash Mitigations in Windows 8.1, describes the latest mitigation techniques Microsoft is incorporating in the latest versions of Windows. He describes the importance of LSASS in his post: (emphasis/bold text is my own) The LSASS Process In …
Aug 25 2014
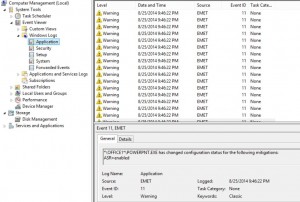
Microsoft Enhanced Mitigation Experience Toolkit (EMET) 5 Protection Methods
Microsoft Enhanced Mitigation Experience Toolkit (EMET) v5 security technology which I outlined in a previous post has several protection methods which will be detailed here. According to my sources at Microsoft 😉, EMET can be installed on workstations and servers (testing is always highly recommended before placing in production). Given the tremendous security improvements when …

Recent Comments