PowerShell provides an easy method to bypass antivirus and other protection methods: Up until several months ago, I was a member of a penetration test team tasked with compromising data centers and evading detection. Industry standard tools such as Metasploit (an attack toolkit that includes a backdoor named Meterpreter) and Mimikatz (a password dumper) …
Category: Microsoft Security
Nov 13 2014
EMET v5.1 Released
This week, Microsoft released version 5.1 of their Enhanced Mitigation Experience Toolkit (EMET). EMET 5.1 can be download from the Microsoft EMET website. Microsoft Security Research and Defense Blog describes the update: Today, we’re releasing the Enhanced Mitigation Experience Toolkit (EMET) 5.1 which will continue to improve your security posture by providing increased application compatibility …
Nov 12 2014
Microsoft’s HeartBleed: The Schannel SSL/TLS vulnerability (MS14-066)
Earlier this year, Unix/Linux/*nix systems dealt with the “Hearbleed” OpenSSL vulnerability which affected a large portion of the web. There is a major vulnerability in Microsoft’s Schannel which was recently patched in MS14-066 (KB2992611). What is SChannel? The Secure Channel (Schannel) security package is a Security Support Provider (SSP) that implements the Secure Sockets Layer …
Nov 10 2014
Kerberos & KRBTGT: Active Directory’s Domain Kerberos Service Account
Every Domain Controller in an Active Directory domain runs a KDC (Kerberos Distribution Center) service which handles all Kerberos ticket requests. AD uses the KRBTGT account in the AD domain for Kerberos tickets. The KRBTGT account is one that has been lurking in your Active Directory environment since it was first stood up. Each Active …
Nov 09 2014
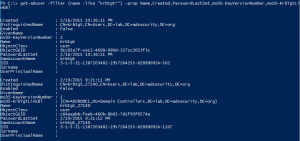
PowerShell Code: Check KRBTGT Domain Kerberos Account Last Password Change
From my GitHub Repo: Get-PSADForestKRBTGTInfo This function discovers all of the KRBTGT accounts in the forest using ADSI and returns the account info, specifically the last password change. Currently, the script performs the following actions: * Queries a Global Catalog in the Active Directory root domain for all KRBTGT accounts in the forest by querying …
Nov 07 2014
The Ultimate Movie Hacking Tool – Command Shell at Windows Logon Screen (via “StickyKeys”)
How many times have you seen a movie where the “hacker” connects to a system with a logon screen, hits a couple of keys, and gets a command shell. Here’s how this can be done for real in Windows. The issue is that the Windows Ease of Use tools are accessible at the logon screen. …
Nov 06 2014
How Attackers Extract Credentials (Hashes) From LSASS
I performed extensive research on how attackers dump credentials from LSASS and Active Directory, including pulling the Active Directory database (ntds.dit) remotely. This information is covered in two newer and greatly expanded posts: How Attackers Dump Active Directory Database Credentials Attack Methods for Gaining Domain Admin Rights in Active Directory Attackers can pull credentials …
Nov 04 2014
BackupExec Service Account Security FAIL
Yes. It actually says that if the BackupExec account is a member of Schema Admins, do not remove! To be fair, it starts off with this Solution which covers the rights required: From Symantec (http://www.symantec.com/business/support/index?page=content&id=TECH88242)
Nov 03 2014
PowerShell for Pentesters
PowerShell is extremely useful for admins. This power is also extremely useful for attackers. There are several PowerShell tools specifically for increasing access on a network: PowerSploit PowerSploit – PowerShell based pentest tool set developed by Mattifestation. PowerSploit is a collection of Microsoft PowerShell modules that can be used to aid reverse engineers, forensic analysts, …
Oct 30 2014
BlueHat 2014 Slides: Reality Bites – The Attacker’s View of Windows Authentication and Post-exploitation
Each year, Microsoft invites security researchers (aka hackers) to speak to Microsoft employees about security issues. One of the most interesting talks listed at “BlueHat” 2014 was the one by the “Pass-the-Hash” experts, Chris Campbell, Bejamin Delpy, and Skip Duckwall. This talk will focus on the how Windows authentication works in the real world and …

Recent Comments