Don’t want your web (cloud) account password to get hacked?
Enable Two-Factor Authentication (aka two-step verification)!
Google Account:
- Visit this site and follow the instructions to configure your cell phone as a second factor
Step 1: You’ll enter your password
Whenever you sign in to Google, you’ll enter your password as usual.
Step 2: You’ll be asked for something else
Then, a code will be sent to your phone via text, voice call, or our mobile app. Or, if you have a Security Key, you can insert it into your computer’s USB port.
Twitter:
- Follow the instructions here.
- Visit your account settings page.
- Select “Require a verification code when I sign in.”
- Click on the link to “add a phone” and follow the prompts.
- After you enroll in login verification, you’ll be asked to enter a six-digit code that we send to your phone via SMS each time you sign in to twitter.com.
Office 365:
Multi-factor authentication increases the security of user logins for cloud services above and beyond just a password. With Multi-Factor Authentication for Office 365, users are required to acknowledge a phone call, text message, or an app notification on their smartphone after correctly entering their password. Only after this second authentication factor has been satisfied can a user sign in.
Multi-factor authentication has been available for Office 365 administrative roles since June 2013, and today we’re extending this capability to any Office 365 user. We’re also enhancing the capabilities that have been available since June. We’re adding App Passwords for users so they can authenticate from Office desktop applications as these are not yet updated to enable multi-factor authentication. And we’re enabling users who are authenticated from a federated on-premises directory to be enabled for multi-factor authentication.
This addition of multi-factor authentication is part of our ongoing effort to enhance security for Office 365, and we’re already working on Office desktop application improvements to Multi-Factor Authentication for Office 365, which we’ll introduce later in this post. Office 365 offers many robust built-in security features for all customers and also optional controls that enable subscribers to customize their security preferences. More information about security in Office 365 is available in the Office 365 Trust Center.
Microsoft Account:
- Microsoft enabled a security code for enhanced security.
Two-step verification uses two ways to verify your identity whenever you sign in to your Microsoft account:
Your password
An extra security code
Two-step verification helps protect your account by making it more difficult for a hacker to sign in, even if they’ve somehow learned your password. If you turn on two-step verification, you’ll see an extra page every time you sign in on a device that isn’t trusted. The extra page prompts you to enter a security code to sign in. We can send a new security code to your phone or your alternate email address, or you can obtain one through an authenticator app on your smartphone.
LinkedIn:
- Instructions for enabling two-step verification with SMS (text message) here:
To turn on two-step verification:
- Move your cursor over your profile photo at the upper right of your homepage and select Privacy & Settings. For verification purposes, you may need to sign in again.
- Click the Account side tab by the shield icon towards the bottom of the page and select Manage security settings.
- Click Turn On under the Two-step verification section.
- Enter your cell phone number to receive a verification code.
- Click Send Code.
- Once you receive the code sent to your phone, enter it into the box on the device you’re using to sign.
- Click Verify.
- Click Done.
GitHub:
- TFA is available for enhanced authentication security with several available methods.
Configuring authentication via a TOTP mobile app
We recommend authenticating with a Time-based One-Time Password (TOTP) application, which automatically generates an authentication code that changes after a certain period of time. TOTP applications are more reliable than SMS, especially for locations outside the US. For more information, see Configuring two-factor authentication via a TOTP mobile app.
Configuring authentication via text message
If you’re unable to authenticate using a TOTP mobile app, you may be able to generate codes using SMS. This method isn’t recommended for non-US numbers; before configuring authentication via SMS, review our list of countries where GitHub supports authentication via SMS. For more information, see Configuring two-factor authentication via text message.
Saving your recovery codes
After successfully setting up 2FA, you’ll be provided a set of randomly generated recovery codes that you should view and save. We strongly recommend saving your recovery codes immediately. If you don’t, though, you can download them at any point after enabling two-factor authentication. For more information, see Downloading your two-factor authentication recovery codes.
Specifying a fallback SMS number
You can provide a second number for a fallback device. If you lose access to both your primary device and your recovery codes, a backup SMS number can get you back in to your account.
Changing authentication delivery methods
You can always switch between receiving authentication codes through a text message or a mobile application.
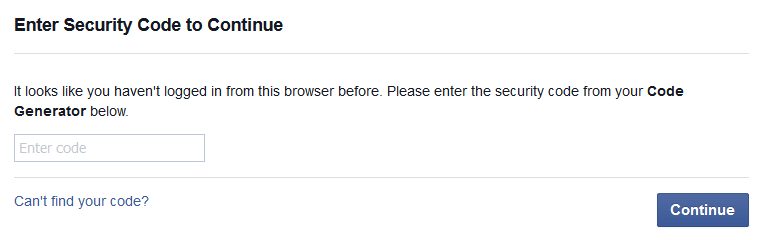
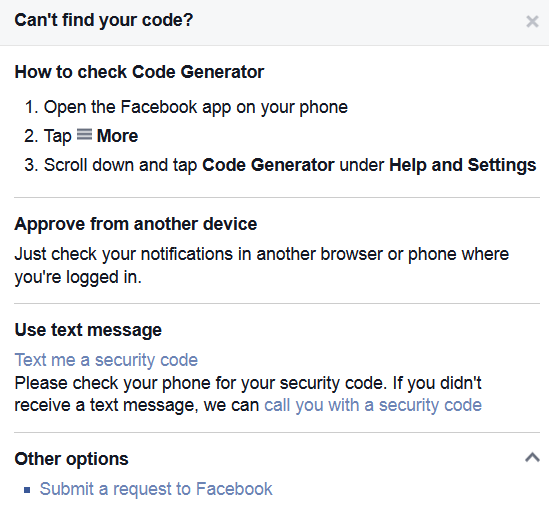
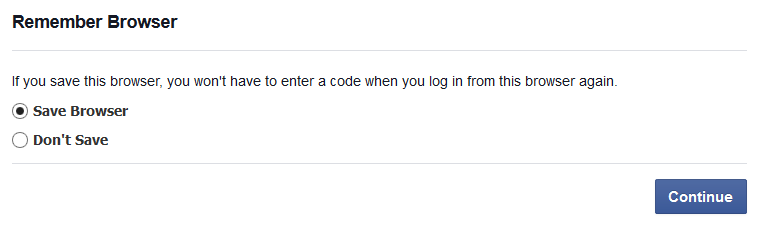
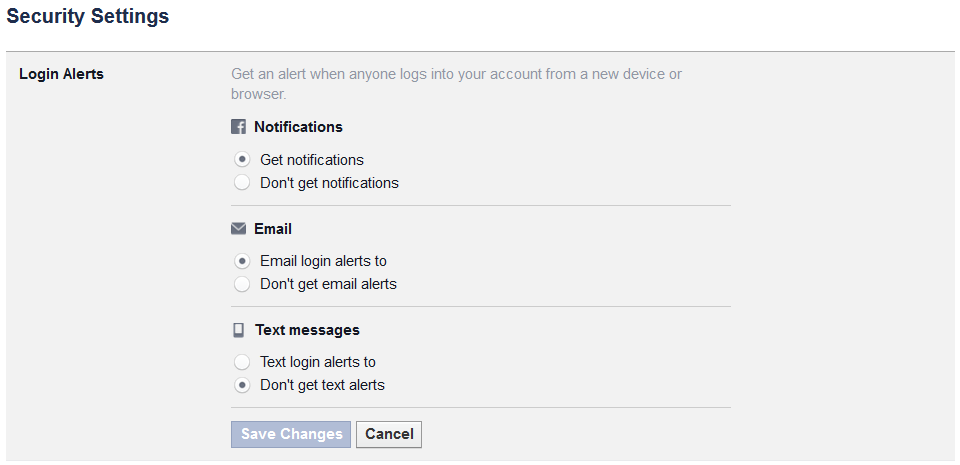
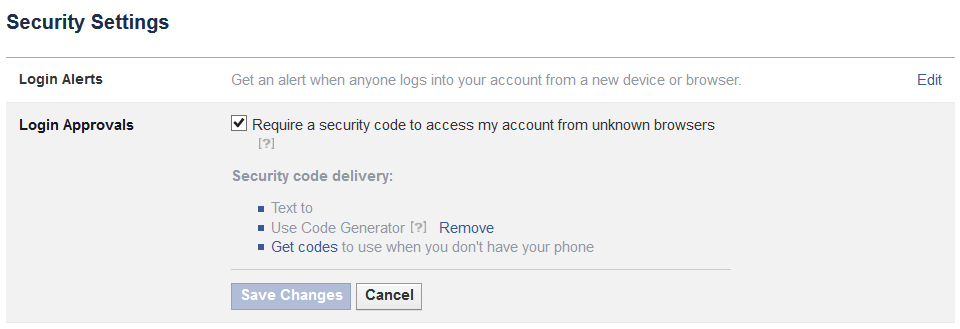
Facebook:
- Facebook enabled a second factor check for logons from new devices a few years back.
Slack:
Slack Two Factor Authentication (TFA) supports both an authenticator app and SMS (text) messages.
Enabling two-factor authentication
Two-factor authentication (2FA) adds an extra layer of security to your Slack account by requiring access to your phone when you log in. With 2FA enabled, you can rest easy: Only you can log into your Slack account, even if your password is compromised or stolen.
Here’s how it works:
- Whenever you sign in to Slack, you’ll be prompted to enter a verification code along with your normal password.
- You’ll either receive a text message from Slack with your authentication code, or easily generate your code using an authentication app on your mobile phone.
- Enter the code in Slack, and that’s it! You’ll be logged into Slack as usual, with added peace of mind.

Recent Comments