In my previous post, “Detecting Kerberoasting Activity” I explain how Kerberoasting works and describe how to detect potential Kerberoasting activity. The trick to this is understanding what activity is normal in order to filter out the noise and increase the fidelity of the alert. This post describes how to filter from millions of events to …
19 results for kerberoast
Feb 05 2017
Detecting Kerberoasting Activity
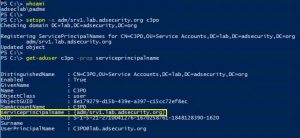
Introduction Kerberoasting can be an effective method for extracting service account credentials from Active Directory as a regular user without sending any packets to the target system. This attack is effective since people tend to create poor passwords. The reason why this attack is successful is that most service account passwords are the same length …
Dec 31 2015
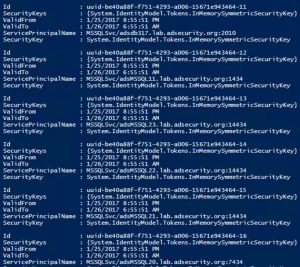
Cracking Kerberos TGS Tickets Using Kerberoast – Exploiting Kerberos to Compromise the Active Directory Domain
Microsoft’s Kerberos implementation in Active Directory has been targeted over the past couple of years by security researchers and attackers alike. The issues are primarily related to the legacy support in Kerberos when Active Directory was released in the year 2000 with Windows Server 2000. This legacy support is enabled when using Kerberos RC4 encryption …
Attack Defense & Detection
This page is meant to be a resource for Detecting & Defending against attacks. I provide references for the attacks and a number of defense & detection techniques. Active Directory & Windows Security ATTACK AD Recon Active Directory Recon Without Admin Rights SPN Scanning – Service Discovery without Network Port Scanning Beyond Domain Admins – …
May 01 2017
BSides Charm (2017) Talk Slides Posted – Detecting the Elusive: Active Directory Threat Hunting
I recently presented my talk “Detecting the Elusive: Active Directory Threat Hunting” at BSides Charm in Baltimore, MD. Slides are now posted in the Presentations section. I cover some of the information I’ve posted here before: PowerShell Security Detecting Kerberoasting: Part 1 and Part 2 On Sunday, April 30th, 2017, I spoke at BSides Charm in …
Nov 03 2016
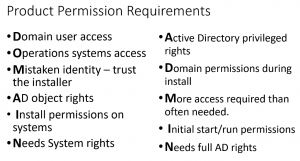
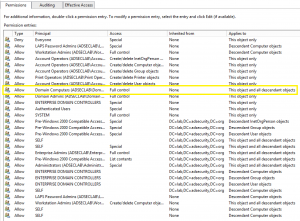
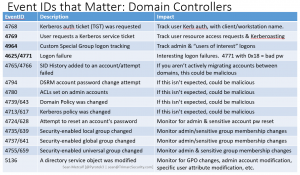
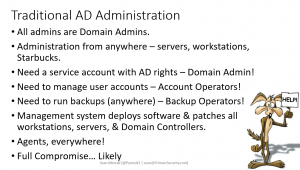
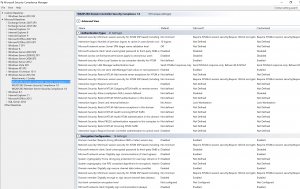
Securing Domain Controllers to Improve Active Directory Security
Active Directory security effectively begins with ensuring Domain Controllers (DCs) are configured securely. At BlackHat USA this past Summer, I spoke about AD for the security professional and provided tips on how to best secure Active Directory. This post focuses on Domain Controller security with some cross-over into Active Directory security. The blog is called …
- 1
- 2


Recent Comments