ADSecurity.org’s Unofficial Guide to Mimikatz & Command Reference page is updated for the new modules/features in Mimikatz v2.1 alpha 20160229. According to Mimikatz author, Benjamin Delpy, the following updates are included in the most recent Mimikatz version(s): Mimikatz Release Date: 2/29/2016 2.1 alpha 20160229 (oe.eo) edition System Environment Variables & other stuff [new] System Environment …
Category: Technical Reference
Mar 01 2016
ADSecurity.org Now Sponsored by Trimarc!
Sean has founded a new security company called Trimarc focused on providing enterprise security solutions. Launching today, Trimarc’s mission is to identify ways to better protect organizations from modern threats not effectively stopped by traditional security measures. ADSecurity.org will continue thanks to Trimarc! Check out Trimarc’s capabilities at TrimarcSecurity.com.
Feb 24 2016
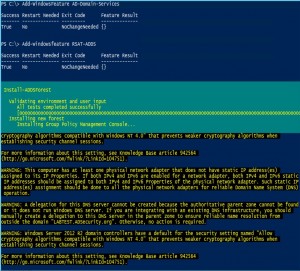
PowerShell Version 5 is Available for Download (again)
After about two months of Microsoft PowerShell developers working around the clock (probably), the bug that wound up causing the WMF 5.0 RTM installer to be pulled is now fixed. There was an issue with the original release dealing with PSModulePath ($Env:PSModulePath) which was reset to default after installation of the original PowerShell v5 installer. …
Feb 11 2016
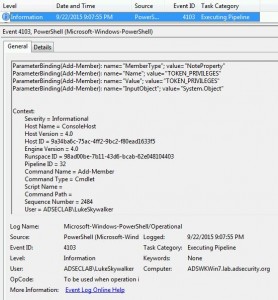
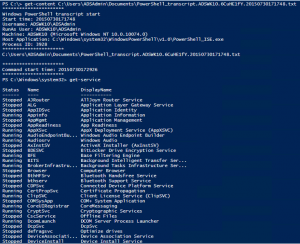
Detecting Offensive PowerShell Attack Tools
At DerbyCon V (2015), I presented on Active Directory Attack & Defense and part of this included how to detect & defend against PowerShell attacks. Update: I presented at BSides Charm (Baltimore) on PowerShell attack & defense in April 2016. More information on PowerShell Security: PowerShell Security: PowerShell Attack Tools, Mitigation, & Detection The most …
Feb 11 2016
PowerShell Version 5 Security Enhancements
PowerShell version 5 is RTM (As of 12/18/2015). Prior to this there was a “production preview” available since August which means it was supported, but not final. With the final release of PowerShell v5 now available, I highly recommend you download PowerShell v5 and start testing to prepare for production deployment. While the PowerShell v5 …
Jan 03 2016
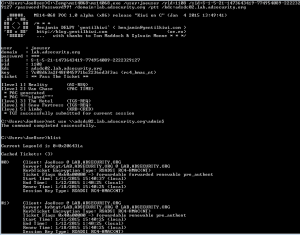
How Attackers Dump Active Directory Database Credentials
I previously posted some information on dumping AD database credentials before in a couple of posts: “How Attackers Pull the Active Directory Database (NTDS.dit) from a Domain Controller” and “Attack Methods for Gaining Domain Admin Rights in Active Directory“. This post covers many different ways that an attacker can dump credentials from Active Directory, both …
Jan 01 2016
Attack Methods for Gaining Domain Admin Rights in Active Directory
There are many ways an attacker can gain Domain Admin rights in Active Directory. This post is meant to describe some of the more popular ones in current use. The techniques described here “assume breach” where an attacker already has a foothold on an internal system and has gained domain user credentials (aka post-exploitation). The …
Dec 31 2015
Cracking Kerberos TGS Tickets Using Kerberoast – Exploiting Kerberos to Compromise the Active Directory Domain
Microsoft’s Kerberos implementation in Active Directory has been targeted over the past couple of years by security researchers and attackers alike. The issues are primarily related to the legacy support in Kerberos when Active Directory was released in the year 2000 with Windows Server 2000. This legacy support is enabled when using Kerberos RC4 encryption …
Dec 28 2015
Finding Passwords in SYSVOL & Exploiting Group Policy Preferences
At Black Hat and DEF CON this year, I spoke about ways attackers go from Domain User to Domain Admin in modern enterprises. Every Windows computer has a built-in Administrator account with an associated password. Changing this password is a security requirement in most organizations, though the method for doing so is not straight-forward. A …



Recent Comments