I improve security for enterprises around the world working for TrimarcSecurity.com Read the About page (top left) for information about me. :) https://adsecurity.org/?page_id=8
Author's posts
Feb 05 2017
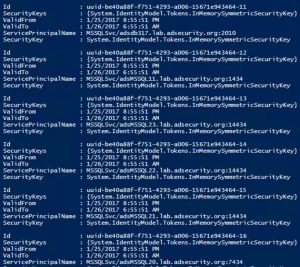
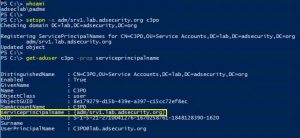
Detecting Kerberoasting Activity
Introduction Kerberoasting can be an effective method for extracting service account credentials from Active Directory as a regular user without sending any packets to the target system. This attack is effective since people tend to create poor passwords. The reason why this attack is successful is that most service account passwords are the same length …
Nov 03 2016
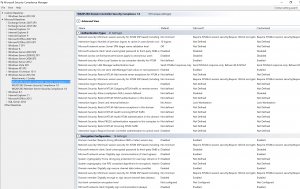
Securing Domain Controllers to Improve Active Directory Security
Active Directory security effectively begins with ensuring Domain Controllers (DCs) are configured securely. At BlackHat USA this past Summer, I spoke about AD for the security professional and provided tips on how to best secure Active Directory. This post focuses on Domain Controller security with some cross-over into Active Directory security. The blog is called …
Oct 18 2016
BSides DC (2016) Talk – PowerShell Security: Defending the Enterprise from the Latest Attack Platform
This Saturday at BSides DC, I am presenting on the current state of PowerShell security in a talk called, “PowerShell Security: Defending the Enterprise from the Latest Attack Platform.” I cover some of the information I’ve posted here before: PowerShell Version 5 Security Enhancements PowerShell Security: PowerShell Attack Tools, Mitigation, & Detection Detecting Offensive PowerShell …
Sep 27 2016
Some Favorite DerbyCon 6 Talks (2016)
This post is a collection of my favorite and interesting talks from DerbyCon 6 (2016). There were a lot of great talks and as I discover them, I’ll add them here. My goal is to collect and provide the talk videos and slides together for a single, easy reference. I’m sure I missed a few. …
Sep 13 2016
DerbyCon 6 (2016) Talk – Attacking EvilCorp: Anatomy of a Corporate Hack
Next week at DerbyCon 6, Will Schroeder (aka Will Harmjoy, @Harmj0y) & I are presenting on enterprise security, “Attacking EvilCorp: Anatomy of a Corporate Hack.” We call this one the “How You Got Hacked” presentation. The company and events are fictional. The techniques are real. On Saturday, September 24th, 2016, Will & I are speaking …
Aug 15 2016
Microsoft LAPS Security & Active Directory LAPS Configuration Recon
Over the years, there have been several methods attempted for managing local Administrator accounts: Scripted password change – Don’t do this. The password is exposed in SYSVOL. Group Policy Preferences. The credentials are exposed in SYSVOL. Password vault/safe product (Thycotic, CyberArk, Lieberman, Quest, Exceedium, etc). Microsoft Local Administrator Password Solution (LAPS). LAPS Overview Microsoft’s …
Aug 13 2016
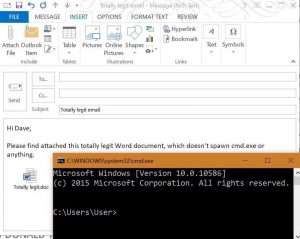
PowerShell Security: PowerShell Attack Tools, Mitigation, & Detection
This post is a follow-up of sorts from my earlier posts on PowerShell, my PowerShell presentation at BSides Baltimore, and my presentation at DEF CON 24. Hopefully this post provides current information on PowerShell usage for both Blue and Red teams. Related posts: BSides Charm Presentation Posted: PowerShell Security: Defending the Enterprise from the Latest …

Recent Comments