PowerShell is a compelling method for attackers (and pentesters) since code is run in memory and there is no reason to touch disk (unlike executables, batch files, and vbscripts). Projects like PowerSploit and POSHSec prove that PowerShell is the future of attacks. PowerShell Magazine has a great article on Investigating PowerShell Attacks: Prior articles by …
Category: Security
Sep 06 2014
The Evolution of Protected Processes Part 1: Pass-the-Hash Mitigations in Windows 8.1
Pass-the-Hash has been around for years The post on Alex Ionescu’s blog, The Evolution of Protected Processes Part 1: Pass-the-Hash Mitigations in Windows 8.1, describes the latest mitigation techniques Microsoft is incorporating in the latest versions of Windows. He describes the importance of LSASS in his post: (emphasis/bold text is my own) The LSASS Process In …
Sep 05 2014
Hacking with PowerShell
Chinese hackers, aka “Deep Panda”, leverage PowerShell while compromising US think-tank computer systems. Recently, we detected breaches of these networks via the use of powershell scripts deployed by the adversary as scheduled tasks on Windows machines. The scripts are passed to the powershell interpreter through the command line to avoid placement of extraneous files on …
Aug 27 2014
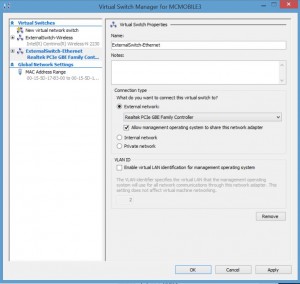
Installing Kali Linux on Windows 8 Hyper-V
Installing Kali Linux on Windows 8 Hyper-V (Windows 8.1 includes improvements to the Hyper-V platform) Installing Hyper-V: Requirement: Windows 8 Pro or Windows 8 Enterprise which include Client Hyper-V. Requirement: Your computer processor must support virtualization technology (VT), though most processors in the past 5 years support VT (pretty much all Intel i-series processors, i3, …
Aug 26 2014
Black Hat 2014 Talk on TSA System Insecurity: Pulling the Curtain on Airport Security
Billy Rios explains how security-focused agencies keep making the same mistakes – this time it’s the TSA. Some of the issues identified in the talk: Network cable connections easily accessible by the public Hardcoded passwords in body scanner systems (which run Windows 98/WinXP) Accounts are stored in a config file. Network services enabled.(with hardcoded passwords) …
Aug 25 2014
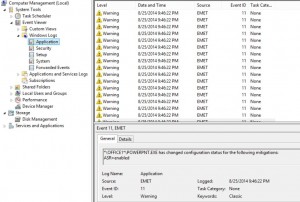
Microsoft Enhanced Mitigation Experience Toolkit (EMET) 5 Protection Methods
Microsoft Enhanced Mitigation Experience Toolkit (EMET) v5 security technology which I outlined in a previous post has several protection methods which will be detailed here. According to my sources at Microsoft 😉, EMET can be installed on workstations and servers (testing is always highly recommended before placing in production). Given the tremendous security improvements when …
Aug 20 2014
Microsoft EMET 5 Released
Microsoft’s EMET (Enhanced Mitigation Experience Toolkit) is a free download from Microsoft that enhances Windows security by preventing common malware and exploitation software methods. It does need to be well-tested before deployment, but there are several legacy Windows methods leveraged by malware to get into a system and take control. Installing EMET provides very strong protection …
Aug 13 2014
Apple iOS Security Whitepaper
In February of this year, 2014, Apple released an updated whitepaper describing Apple iOS Security. Overall, the operating system and its components are very securely designed. The Table of Contents: Introduction System Security Secure Boot Chain System Software Authorization Secure Enclave Touch ID Encryption and Data Protection Hardware Security Features File Data Protection Passcodes Data …
Jul 11 2014
Real-Time World Hack Map
This is an incredible map of the world that shows real-time network attacks. The animation makes it look like something out of the movie, “WarGames.” Most impressive. http://map.ipviking.com/?_ga=1.106938115.1477390587.1388686673#
May 20 2014
Microsoft BlueHat Resources
Microsoft has their own internal employee security conference called “BlueHat“. Here are session links from the past few years:

Recent Comments